Shadow IoT in the Enterprise: The Hidden Devices Putting Your Business at Risk in 2026
58% of IoT devices in enterprise environments are unmanaged, creating a silent invasion and potential backdoor for attackers.
Page 5 of 20

58% of IoT devices in enterprise environments are unmanaged, creating a silent invasion and potential backdoor for attackers.
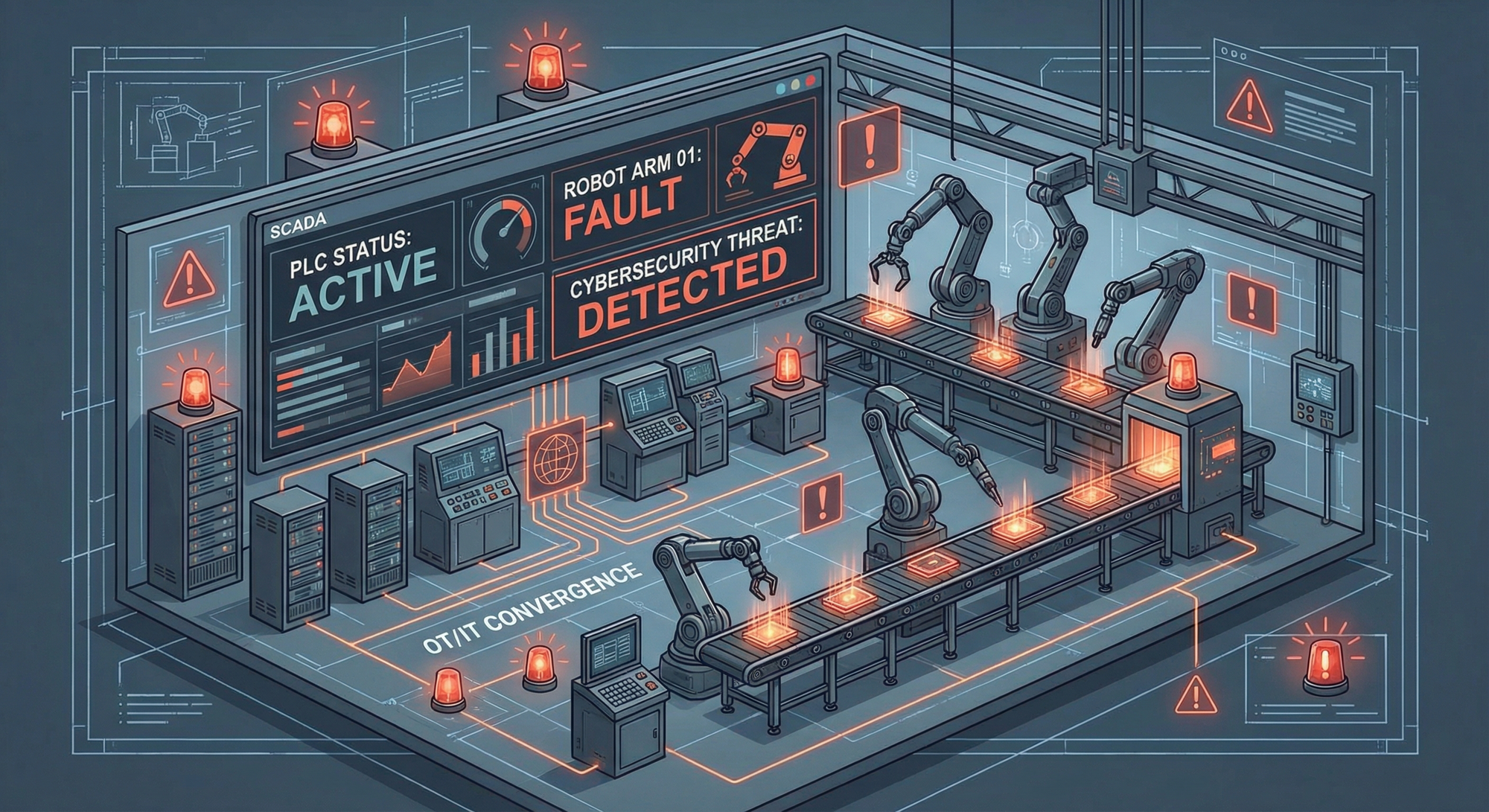
Manufacturing IoT is under sustained attack. From ransomware shutting down production lines to nation-state actors pre-positioning in OT networks, here are the security risks every industrial business must address in 2026.



The EU Data Act officially became applicable on September 12, 2025, and it represents a paradigm shift for businesses operating connected devices.





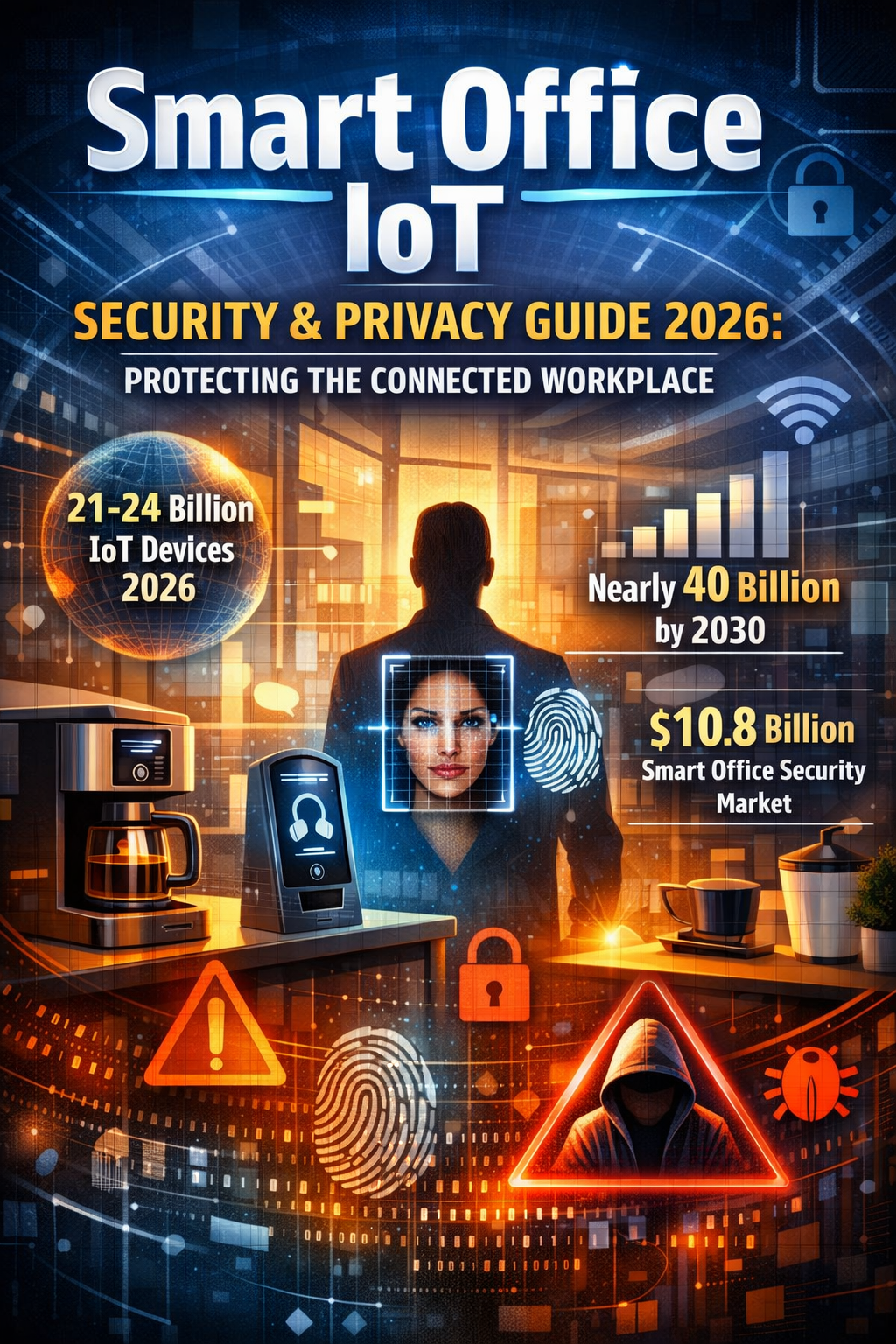
The smart office market is exploding, but IoT attacks surged 124% in 2024, creating a security crisis with hybrid work blurring security perimeters.
