The modern world relies heavily on critical infrastructure – the foundational assets and systems that underpin societal functions, from energy and water to healthcare and transportation. However, this very infrastructure is facing an increasingly sophisticated and interconnected threat landscape, where cyber-attacks can have devastating physical consequences and physical breaches can lead to significant cyber disruptions. In this era of connected systems and hybrid threats, the traditional siloed approach to security, where cybersecurity and physical security are handled in isolation, creates significant vulnerabilities and leaves critical infrastructure dangerously exposed. This article delves into the imperative need for security convergence, exploring the limitations of security silos, the compelling benefits of a holistic strategy, the inherent challenges in achieving this integration, and the pathways towards a more resilient future for our essential infrastructure.
The Evolving Threat Landscape: From Silos to Synergy
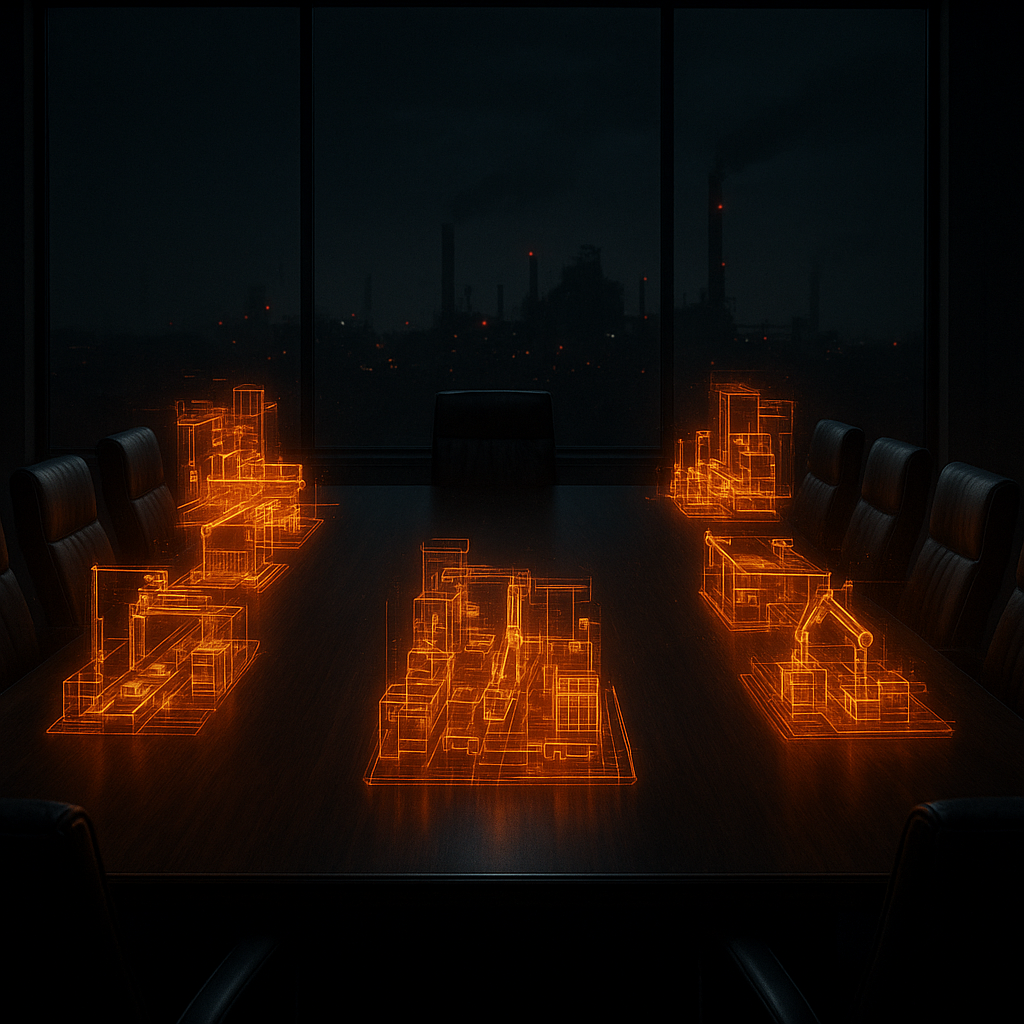
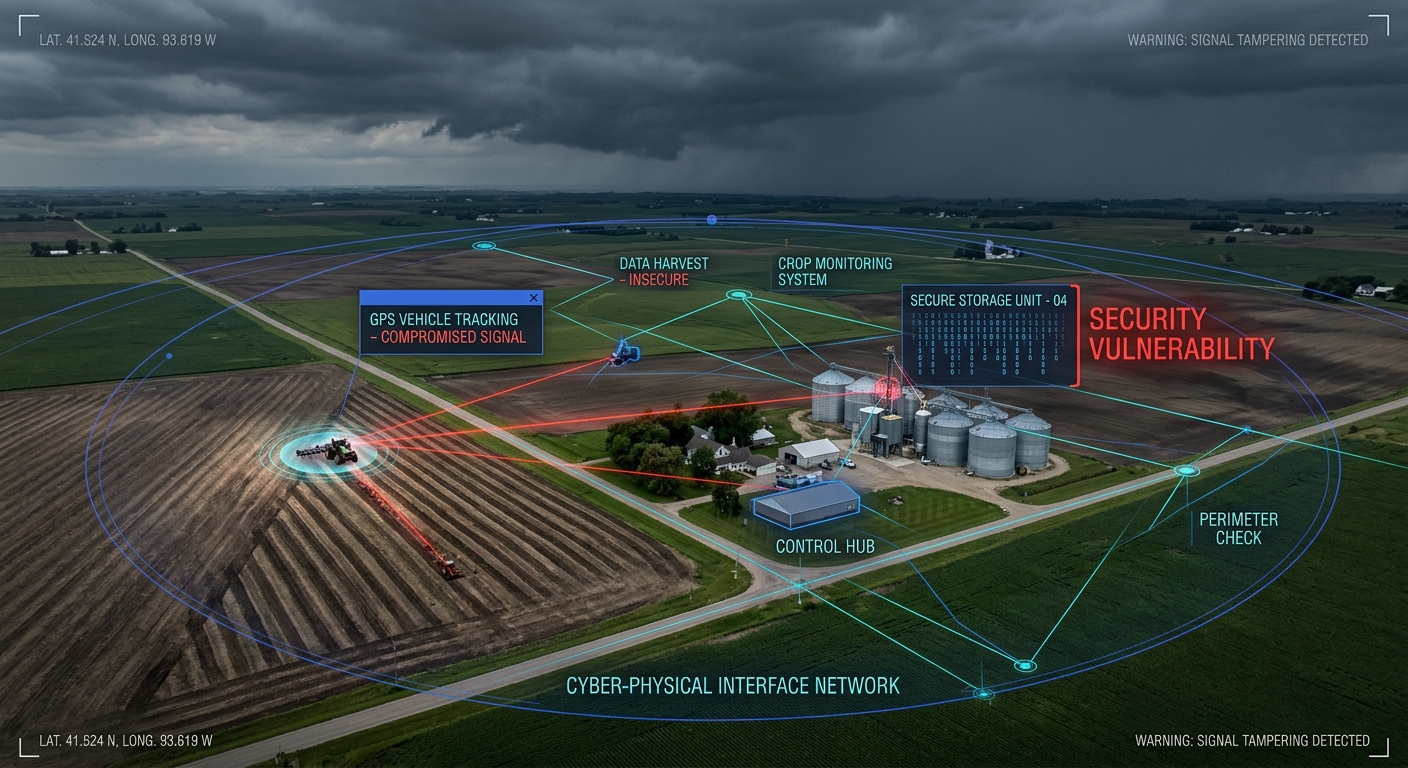
For years, cybersecurity and physical security have operated as distinct domains, each with its own expertise, tools, and priorities. Physical security focused on tangible threats like unauthorized access, while cybersecurity addressed digital risks such as malware and data breaches. However, the increasing interconnectedness of operational technology (OT), information technology (IT), and physical systems has blurred these lines, creating a complex cyber-physical environment. This interconnectedness, driven by the pursuit of efficiency, automation, and enhanced capabilities through technologies like the Internet of Things (IoT) and Industrial Internet of Things (IIoT), has simultaneously expanded the attack surface and created new avenues for malicious actors.
Examples like the Stuxnet attack, which physically damaged Iranian centrifuges by exploiting digital vulnerabilities, and attacks on Saudi Aramco and Ukrainian power grids starkly illustrate the potential for cyber incidents to have real-world physical impacts. Conversely, inadequate physical security can provide easy access for adversaries to compromise network systems, as demonstrated in penetration tests where unauthorized physical access led to control over critical data and operational systems. These “hybrid” or “blended” threats, arising from the intersection of cyber and physical domains, exploit the seams between traditionally separate security functions.
The Perils of Protection in Isolation: The Vulnerability of Security Silos
The continued management of security in silos, where physical and cybersecurity teams operate independently with limited communication and coordination, presents a major impediment to effective protection. This lack of a comprehensive perspective results in several critical shortcomings:
- Unrecognized Vulnerabilities and Gaps: Siloed teams may be unaware of how a vulnerability in one domain can be exploited to compromise another. The “glue” holding together disparate security measures often becomes the weakest point, easily exploited by attackers who understand these interdependencies.
- Ineffective Prioritization and Resource Allocation: Without a holistic understanding of risk, organizations struggle to accurately set security priorities and allocate resources effectively. Funding and attention may be disproportionately focused on threats within a specific domain, neglecting more significant risks that span both cyber and physical realms.
- Failure to Address Interconnected Systems: Silos hinder the ability to address the vulnerabilities of connected physical-cyber systems. As OT systems become increasingly integrated with IT networks, threats can propagate across these boundaries. Isolated security teams may lack the visibility and understanding to effectively defend against such cross-domain attacks.
- Duplication of Effort and Inefficiencies: Independent security teams may unknowingly duplicate efforts in areas like investigations, technology procurement, and data management, leading to inefficiencies and increased costs.
- Lack of Shared Situational Awareness: Siloed operations result in a fragmented view of the overall security posture. Teams may be unsure whether a physical breach led to a cyberattack or vice versa, hindering effective incident response and threat analysis.
- Cultural and Communication Barriers: As highlighted in our previous discussion, significant cultural differences, varying vocabularies, and differing priorities between IT and physical security teams act as barriers to collaboration and information sharing.
- Resistance to Change and “Turf Wars”: Departments may resist closer collaboration due to concerns about losing autonomy or resources, perpetuating the “turf wars” that undermine unified security efforts.
The Promise of Integration: Benefits of Security Convergence
Recognizing the limitations of siloed security, a growing consensus emphasizes the critical need for security convergence – a holistic approach that strategically aligns and integrates physical and cybersecurity functions. This convergence offers numerous compelling benefits for protecting critical infrastructure:
- Enhanced Understanding of Risk: Convergence allows for a comprehensive view of organizational risk, considering the interconnectedness of cyber and physical threats. Joint risk assessments that consider both domains enable organizations to identify and prioritize the most critical vulnerabilities and potential consequences.
- Improved Threat Detection and Response: A unified approach facilitates better information sharing and collaboration between security teams, leading to more effective detection, analysis, and response to hybrid threats. Technologies like Converged Security and Information Management (CSIM) systems can integrate data from various physical and IT security applications, providing a unified view of security events.
- Strategic Alignment and Resource Optimization: Convergence enables organizations to align security strategies and spending based on overall risk priorities. This can lead to the elimination of duplicate efforts, streamlined processes, and more efficient use of resources.
- Enhanced Operational Resilience: By breaking down silos, security convergence contributes to a broader goal of operational resilience, recognizing that disruptions, regardless of their origin (cyber, physical, or natural), need a coordinated response. Closer collaboration between security and other resilience functions like disaster recovery and business continuity becomes possible.
- Improved Regulatory Compliance: A converged security model with standardized policies and procedures can facilitate adherence to various regulatory requirements related to both physical and cybersecurity. Centralized accountability for security also aligns with the principles of many regulations.
- Stronger Security Culture: Integrated security efforts can foster a more security-conscious culture across the organization, where employees understand the interconnectedness of security risks and their role in maintaining a robust defense.
- Better Metrics and Accountability: Converged security allows for the development of holistic security metrics that reflect the overall security posture and progress towards organizational goals, fostering greater accountability across all security functions.
Navigating the Obstacles: Challenges in Achieving Convergence
Despite the clear advantages, achieving true convergence between IT and physical security is not without significant challenges:
- Deep-Rooted Cultural Differences: Overcoming the distinct cultures, perspectives, and vocabularies of IT and physical security teams requires deliberate efforts to foster understanding, communication, and shared goals.
- Organizational Inertia and Siloed Structures: Dismantling long-established security silos and restructuring organizations to promote integration can face resistance and require strong leadership commitment.
- Technical Integration complexities: Integrating disparate physical security systems (e.g., access control, video surveillance) with IT security tools and networks can be technically challenging and may involve integrating legacy OT systems with modern IT infrastructure.
- Resistance to Role Changes and “Turf Battles”: Concerns about job security, loss of authority, and departmental “turf wars” can impede collaboration and the creation of unified security roles and responsibilities.
- Skill Gaps and the Need for Cross-Training: Building a security workforce with expertise that bridges both IT and physical security domains requires investment in cross-training and the recruitment of professionals with a broader understanding of security risks.
- Lack of Common Terminology and Frameworks: The absence of common terminology and standardized frameworks that span both physical and cyber security can hinder effective communication and the development of unified strategies.
- Differing Priorities and Risk Appetites: IT and physical security teams may have historically focused on different priorities (e.g., data confidentiality vs. physical access control) and may have varying risk appetites, requiring alignment at a strategic level.
Pathways to Integration: Strategies for Bridging the Divide
Overcoming these challenges and fostering security convergence requires a multifaceted approach:
- Strong Leadership Buy-in: Top-down commitment and leadership alignment are crucial for driving the cultural and organizational changes necessary for convergence. Leaders must champion the vision of a unified security strategy and actively break down silos.
- Establishing Clear Communication Channels: Implementing clear and consistent communication strategies across all security functions is essential for sharing information, fostering collaboration, and building trust. Creating common terminology can further improve understanding.
- Reorganizing Structures and Roles: Considering the creation of integrated security teams or appointing a single executive (e.g., a Chief Security Officer - CSO) to oversee both physical and cybersecurity can promote a holistic approach. Clearly defining roles and responsibilities in a converged model is critical.
- Implementing Joint Risk Assessments and Penetration Tests: Conducting ** совместные assessments** that consider both cyber and physical vulnerabilities provides a holistic understanding of risk. Similarly, penetration tests that simulate hybrid attacks can reveal weaknesses at the intersection of these domains.
- Developing Integrated Security Metrics: Establishing common security metrics that track progress towards unified goals and provide visibility across both physical and cyber domains is vital for measuring effectiveness and driving continuous improvement.
- Investing in Cross-Training and Education: Providing training and development opportunities that broaden the skill sets of security personnel in both cyber and physical domains is crucial for building a more versatile and collaborative workforce.
- Adopting a Security Convergence Framework: Implementing a structured framework that provides a vehicle for coordinating security risk management across all facets of the organization can help align disparate protection programs and clarify responsibilities.
- Leveraging Technology for Integration: Implementing technology solutions that facilitate information sharing and collaboration across security functions, such as CSIM systems, can help bridge the gap between disparate systems and teams.
- Reimagining Public-Private Partnerships (PPPs): For critical infrastructure where the private sector plays a significant role, PPPs should be designed from the outset with a holistic cyber-physical security perspective, emphasizing quality, training, and information sharing.
The Role of Legislation and Standards
The European Union, as highlighted in the sources, is actively developing legislation and standards relevant to cyber-physical security. Directives like NIS2 (Network and Information Security Directive) and the CER (Directive on the Resilience of Critical Entities) aim to enhance both cyber and physical resilience. While these are handled in separate texts, there is recognition of the need for parallel considerations and cross-referencing. Furthermore, standards like EN IEC 62443 (Cyber Security Standard for Operational Technology) and the EN 17483 series (Private Security Services – CIP) provide frameworks and quality criteria relevant to protecting cyber-physical systems and critical infrastructure. Future iterations of these standards will likely further emphasize the need for a holistic approach.
Conclusion: Embracing a Holistic Future for Critical Infrastructure Security
The era of treating cybersecurity and physical security as separate entities is no longer tenable in the face of increasingly sophisticated and interconnected threats to critical infrastructure. Security convergence is not merely a desirable outcome but a fundamental necessity for ensuring the resilience and protection of the essential systems that underpin our societies. By actively breaking down security silos, fostering communication and collaboration, addressing cultural differences, and implementing holistic strategies and frameworks, organizations can move towards a future where cyber and physical security work in concert to create a truly robust defense against the evolving threat landscape. This integrated approach is essential for safeguarding our nations, economies, and the well-being of citizens in an increasingly connected world.