The greatest industrial transformation in decades is also the greatest cybersecurity risk. Here’s what operations leaders need to know—and do.
For decades, the digital world and the physical world existed in parallel universes. Your corporate network handled emails, spreadsheets, and customer databases. Your industrial control systems—the programmable logic controllers, sensors, and SCADA systems that actually make things—operated in splendid isolation, air-gapped from the chaos of the internet.
That wall is now gone.
The Industrial Internet of Things (IIoT) market is projected to exceed $1.5 trillion by 2030, according to industry analysts. IT/OT convergence technologies alone represent a market approaching $100 billion by 2030, roughly doubling from 2024 levels. Today, the majority of industrial organizations have adopted some form of IT/OT convergence, driven by promises of predictive maintenance, real-time operational visibility, and competitive necessity.
But here’s the number that should keep operations leaders awake: 73% of organizations experienced an OT-impacting breach in 2024—up from 49% the prior year. Manufacturing ransomware incidents have cost $17 billion in downtime since 2018. When production stops, losses average $1.9 million per day. For some facilities, unplanned downtime reaches $125,000 per hour.
The convergence of IT and OT isn’t a future trend. It’s happening now. And for every efficiency gained, a new attack vector has opened.
This isn’t a story about technology. It’s a story about two fundamentally different cultures—IT and OT—being forced into an arranged marriage while adversaries watch for the vulnerabilities that emerge. Understanding this IT/OT convergence security challenge, and navigating it successfully, has become an existential imperative for every business that relies on operational technology.
The IT/OT Culture Clash: When Two Worlds Collide
To understand why IT/OT convergence creates such profound security challenges, you first have to understand that these two worlds were never designed to coexist.
Information Technology operates on the CIA principle: Confidentiality first, then Integrity, then Availability. IT systems get refreshed every 3-5 years. Patches roll out weekly. Constant change is normal. If something breaks, you restore from backup and users grumble about downtime.
Operational Technology operates on the exact opposite principle—AIC: Availability first, then Integrity, then Confidentiality. That programmable logic controller managing a chemical process might be 20 years old, running software that hasn’t been updated since the Bush administration. And that’s by design. In OT environments, any change—including security patches—is high-risk. Changes might require shutting down production lines. In some cases, they could affect physical safety. The mantra is: if it works, don’t touch it.
Now imagine connecting these two worlds together.
When you bridge IT and OT networks to enable real-time data analytics, predictive maintenance, and cloud-based operational intelligence, you’re simultaneously:
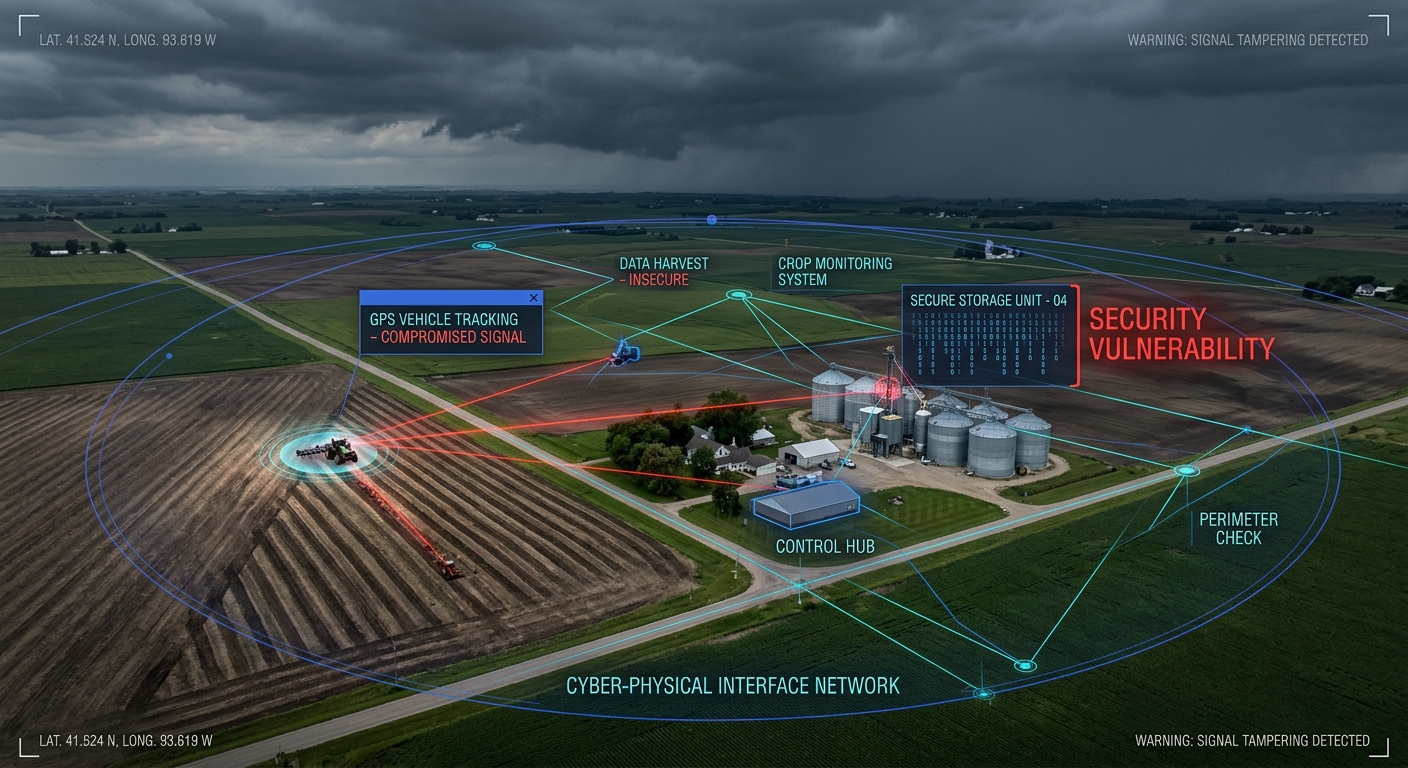
- Expanding the attack surface exponentially. Claroty’s research found that 40% of industrial organizations have assets insecurely connected to the internet. Another 12% have OT assets actively communicating with malicious domains.
- Inheriting IT’s patching expectations without OT’s ability to patch. Those legacy systems that can’t be updated? They’re now reachable from corporate networks that face constant attack.
- Creating cascade pathways. A ransomware attack on your IT billing system can now propagate into—or force the shutdown of—your entire operational environment.
- Multiplying third-party risks. Every vendor with access to your IT network potentially has a pathway to your OT systems. The SolarWinds and MOVEit attacks demonstrated how supply chain compromises cascade across thousands of organizations.
The authentication gap makes this worse. Many OT systems still use factory default credentials. Multifactor authentication is rare. Communication channels often lack encryption. These weren’t oversights when these systems were designed for isolated networks. They become catastrophic vulnerabilities when those same systems connect to enterprise IT.
The uncomfortable truth: By connecting previously air-gapped OT systems to IT networks, organizations have inadvertently created one of the largest attack surfaces in history—comprised largely of systems that cannot be secured using traditional IT methods.
Real-World IT/OT Security Breaches: Lessons from Recent Attacks
The theoretical risks of IT/OT convergence have become very real, very fast. Consider these examples:
Clorox: $49 Million in Disruption
In August 2023, ransomware attackers hit Clorox just before flu season—exactly when demand for cleaning products peaks. The attack disrupted manufacturing operations so severely that the company was forced to manually process orders, slowing operations to a crawl.
The financial toll: $49 million in direct costs, plus product shortages that lasted months. Perhaps most damaging was the revelation that an internal audit in 2020 had warned of cybersecurity flaws at manufacturing plants. The warnings went unheeded.
Colonial Pipeline: 45% of East Coast Fuel Supply
The May 2021 Colonial Pipeline attack has become the canonical example of how IT incidents cascade into OT disasters. The ransomware itself only hit the IT billing network. But because Colonial couldn’t verify what the attackers might have accessed, and couldn’t bill customers for fuel, they made the agonizing decision to shut down the entire pipeline.
The result: 5,500 miles of pipeline offline, 45% of the US East Coast’s fuel supply disrupted, and panic buying at gas stations across the Southeast. Colonial paid a $4.4 million ransom—and proved that attackers don’t need to touch OT systems directly to cause operational catastrophe.
Oldsmar Water Treatment: Minutes from Catastrophe
In February 2021, an attacker accessed the water treatment facility in Oldsmar, Florida, using TeamViewer—a consumer-grade remote access tool. The intruder attempted to increase sodium hydroxide (lye) levels from approximately 100 parts per million to 11,100 parts per million—more than 100 times the normal concentration.
An alert operator noticed the mouse cursor moving on its own and immediately reversed the change before it could take effect. Without that human intervention, the water supply for 15,000 residents could have been poisoned. The vulnerabilities? Shared passwords, outdated Windows 7 systems, and remote access tools never designed for critical infrastructure.
RansomHub and the Gijón Bio-Energy Plant
In May 2024, the RansomHub group attacked a bio-energy plant in Spain, demonstrating that sophisticated attackers can now reach deep into OT networks. The attackers accessed SCADA systems directly and exfiltrated over 400 GB of data—reaching Level 0/1 systems that directly control physical processes.
This wasn’t a theoretical exercise or an IT system that happened to affect operations. This was direct targeting of industrial control systems.
Small Business Reality: When Recovery Isn’t Possible
Not every cyberattack story has a recovery chapter. When smaller companies suffer operational technology disruptions, they often lack the financial reserves, cyber insurance, and recovery capabilities that large enterprises take for granted.
For organizations without the financial resilience of a Clorox, an IT/OT security breach isn’t a setback—it’s an extinction event. Industry estimates suggest that 60% of small businesses close within six months of a significant cyberattack.
The Nation-State Dimension: Volt Typhoon
Perhaps most alarming is the revelation that Chinese state-sponsored actors, known as Volt Typhoon, have been pre-positioning within US critical infrastructure networks for potential future disruption.
FBI Director Christopher Wray testified to Congress: “This threat is not theoretical. CISA teams have found and eradicated Chinese intrusions into critical infrastructure across multiple sectors. What we’ve found to date is likely the tip of the iceberg.”
Volt Typhoon hackers remained in Massachusetts utility systems for ten months before detection. Their targets span electric utilities, telecommunications, water systems, and transportation. Their goal isn’t immediate disruption—it’s having the capability to cause massive damage during a future geopolitical crisis.
Recent ransomware statistics underscore the scale of the threat: industrial entities face hundreds of ransomware incidents quarterly, with manufacturing accounting for roughly two-thirds of cases. North America remains the most heavily targeted region. The threat isn’t slowing down—it’s industrializing, with ransomware-as-a-service operations enabling even unsophisticated attackers to target critical infrastructure.
Bridging the IT/OT Governance Gap: Ownership and Accountability
Here’s a paradox that’s plaguing organizations across every industrial sector: 80% of Chief Information Security Officers now officially oversee OT security. Yet only 35% of organizations report having a mature, fully integrated IT/OT security operations model.
In other words, we’ve assigned responsibility without building capability.
The governance gap exists because IT/OT security doesn’t fit neatly into traditional organizational structures:
The Cultural Divide. IT and OT teams have operated in separate silos for decades. They speak different languages—literally, in terms of protocols, and figuratively, in terms of priorities. IT security professionals may not understand that patching an OT system requires shutting down a production line. OT engineers may view security measures as threats to the uptime they’re measured on.
The Legacy System Problem. Who owns the security of a 20-year-old PLC? It was purchased by Operations, managed by Engineering, and now needs security controls from IT. Budget allocation is unclear. Accountability is murky. The “if it works, don’t touch it” mentality that kept OT systems running safely now conflicts directly with security requirements.
Competing Metrics. IT teams are measured on data protection and compliance. OT teams are measured on uptime and production throughput. When a security change requires shutting down a production line, these metrics collide. Without clear governance, the default is often to delay security in favor of production.
The Skills Shortage. Personnel who understand both IT security frameworks and OT operational requirements are rare. Cross-training programs exist in theory but are often underfunded in practice. Meanwhile, OT security tools require specialized knowledge that traditional IT security teams don’t possess.
Regulatory pressure is forcing clarity. The EU’s NIS2 Directive emphasizes executive-level accountability for cybersecurity—with penalties reaching €10 million or 2% of global annual turnover. Deloitte’s analysis of NIS2’s first year found regulators increasingly focused on evidence of executive oversight, not just technical controls.
Supplier security is also driving change. IEC 62443-4-1 certifications—demonstrating secure development practices—are becoming contract prerequisites. Organizations that can’t demonstrate security maturity are losing bids.
The 2026 reality: The question has evolved from “who is responsible?” to “who is achieving maturity?” Organizations still debating ownership while competitors build capability are falling behind in both security posture and competitive positioning.
Defense in Depth: Segmentation and Zero Trust for IT/OT Convergence
If you can’t prevent convergence (and you can’t—the business case is too compelling), you must architect convergence securely. The foundation is segmentation: ensuring that connections between IT and OT are controlled, monitored, and defensible.
The Purdue Model: Your Architectural Foundation
The Purdue Enterprise Reference Architecture provides the structural framework for understanding where controls belong:
- Levels 5-4 (Enterprise Zone): Corporate network, ERP systems, business applications. Standard IT security applies.
- Level 3.5 (Industrial DMZ): The critical boundary between IT and OT. Data diodes, firewalls, and jump servers control what crosses.
- Level 3 (Site Operations): Engineering workstations, historians, SCADA servers.
- Level 2 (Area Supervisory Control): Human-machine interfaces, supervisory applications.
- Level 1 (Basic Control): PLCs, RTUs, DCS controllers.
- Level 0 (Process): Sensors, actuators, physical equipment.
The fundamental principle: traffic should only flow between adjacent levels through controlled conduits. An accountant’s laptop should never have a direct pathway to a PLC controlling a chemical process.
IEC 62443: The Segmentation Standard
The Purdue Model maps your environment, but IEC 62443 provides the actual security requirements. Two concepts are central:
Zones are groups of assets with similar security requirements. Each zone is assigned a Security Level Target (SL-T) from 1 to 4, based on risk assessment. A zone containing systems that could cause environmental damage or safety incidents requires higher security levels than a zone containing non-critical monitoring equipment.
Conduits are the controlled communication pathways between zones. All traffic flowing between zones must pass through defined conduits with appropriate controls—firewalls, data diodes, or application proxies.
The 2024 updates to IEC 62443 harmonized the standard with ISO/IEC 27001, NIST SP 800-82, and the EU’s NIS2 Directive. The revisions also incorporate practical feedback from real-world implementations and explicitly address the challenge of securing legacy systems with 20+ year lifecycles.
Zero Trust: Beyond Perimeter Defense
Traditional perimeter defense assumes everything inside the network is trusted. That assumption fails catastrophically when:
- 40% of organizations have insecurely internet-connected assets
- Attackers exploit third-party access and supply chain vulnerabilities
- Lateral movement from IT to OT is possible
Zero trust operates on a different principle: never trust, always verify. Implementation for converged environments requires:
Complete Asset Discovery. You cannot protect what you don’t know exists. Inventory all OT assets—including legacy systems, unmanaged devices, and IoT sensors. Map every communication pathway. Identify what processes each device connects to.
Microsegmentation. Create granular security zones around specific assets, prioritized by business impact. Limit lateral movement capability so that compromising one system doesn’t provide access to everything.
Least Privilege Access. Users, devices, and applications receive only the permissions they need—nothing more. Implement MFA for all remote and administrative access. Deploy secure remote access solutions designed specifically for OT environments (not TeamViewer).
Continuous Monitoring. Use passive monitoring tools designed for OT protocols. Analyze traffic patterns for anomalies. Critically, don’t disrupt production with active scanning that can crash legacy systems.
Modern identity-based microsegmentation solutions can learn network behavior and restrict access based on operational needs—often deployable in weeks rather than years, significantly accelerating IT/OT security maturity.
OT Security Compliance: Navigating NIST, IEC 62443, and NIS2 Requirements
Compliance isn’t just a checkbox exercise—it’s increasingly a competitive requirement and a liability shield. Understanding the regulatory landscape helps prioritize security investments.
IEC 62443: The Industrial Gold Standard
IEC 62443 defines cybersecurity requirements across the entire supply chain: asset owners, system integrators, and component manufacturers. Key parts include:
- IEC 62443-2-1 (2024 update): Cybersecurity Management System requirements
- IEC 62443-3-2: Security risk assessment, zones and conduits methodology
- IEC 62443-3-3: System security requirements at each Security Level
- IEC 62443-4-1: Secure development lifecycle for component manufacturers
Compliance approach: Start with asset mapping, define zones and conduits based on risk analysis, then determine target security levels for each zone. Use the gaps between current state and target state to prioritize investments.
NIST Cybersecurity Framework 2.0
The NIST CSF remains the dominant framework in North America—65% of industrial firms are actively aligning according to the SANS 2024 ICS/OT Cybersecurity Survey.
The 2.0 version added a Govern function, recognizing that cybersecurity requires organizational governance, not just technical controls. For IT/OT convergence, the Govern function provides the structure for creating unified risk management strategy.
NIST SP 800-82, the “Guide to Operational Technology Security,” provides specific guidance for ICS environments and complements the broader CSF framework.
NIS2 Directive (EU)
The NIS2 Directive, now in force across EU member states, significantly expands cybersecurity requirements across 18 critical sectors including energy, transport, health, and digital infrastructure.
Key requirements include:
- Risk management measures with documented evidence
- Corporate accountability—executives can be held personally liable
- Incident reporting within 24 hours of detection
- Business continuity planning
- Supply chain security programs
Penalties reach €10 million or 2% of global annual turnover—whichever is higher.
Sector-Specific Requirements
Different industries face additional requirements:
Sector Key Regulations
Energy NERC CIP (North America), IEC 62443
Water America’s Water Infrastructure Act (AWIA)
Healthcare HIPAA (where OT intersects patient data)
Automotive UNECE WP.29, ISO/SAE 21434
General (EU) NIS2, Machinery Regulation
Framework Harmonization
Modern best practice layers frameworks appropriately: IEC 62443 for OT-specific detailed controls, NIST CSF for enterprise risk management umbrella, NIS2 for EU regulatory compliance, and ISO/IEC 27001 for information security management systems.
These frameworks increasingly map to each other, enabling integrated compliance approaches rather than redundant parallel efforts.
IT/OT Security Implementation Roadmap: An 18-Month Action Plan
For operations leaders ready to act, here’s a phased approach that balances urgency with operational reality.
Phase 1: Assessment (Months 1-3)
Asset Discovery & Inventory. Complete inventory of all IT and OT assets, including legacy systems, unmanaged devices, and IoT. Document network topology and communication flows. You will be surprised by what you find—organizations routinely discover 30-40% more connected assets than they expected.
Risk Assessment. Identify crown jewel assets—the systems that absolutely cannot go down. Assess current security posture against IEC 62443 and NIST frameworks. Quantify business impact of downtime in dollars per hour. This financial framing will be essential for securing budget.
Governance Clarification. Define ownership model—unified CISO responsibility or federated model with clear accountabilities. Establish cross-functional IT/OT security team with representatives from both cultures. Most critically: secure executive sponsorship and dedicated budget.
Phase 2: Foundation (Months 4-9)
Segmentation Implementation. Implement the Industrial DMZ (iDMZ) between IT and OT at the Level 4/3 boundary. Define zones based on risk and operational requirements. Deploy firewalls and data diodes at conduit points. Start with the highest-risk pathways first.
Secure Remote Access. Replace consumer-grade remote access tools immediately. Implement OT-specific secure remote access with MFA, session recording, and time-limited access windows. The Oldsmar incident demonstrated that this isn’t optional.
Detection Capabilities. Deploy passive OT network monitoring tools that won’t disrupt operations. Integrate OT alerts into SOC operations—but ensure SOC personnel understand OT context. Establish baseline normal behavior so anomalies become visible.
Phase 3: Maturity (Months 10-18)
Zero Trust Evolution. Implement microsegmentation within OT zones—not just between IT and OT. Deploy identity-based access controls. Enforce least privilege across all connections.
Operational Integration. Cross-train IT security and OT operations staff. Develop OT-specific incident response playbooks that account for operational constraints. Conduct tabletop exercises with both teams—and include plant operations leadership.
Continuous Improvement. Conduct regular vulnerability assessments using passive methods appropriate for OT. Schedule quarterly security reviews with operations leadership. Implement formal supply chain security programs for vendors with OT access.
Justifying the Investment
The business case for IT/OT security is straightforward:
Metric Cost
Average breach cost (industrial sector) $5.4+ million
Downtime per hour (manufacturing) $125,000
Downtime per day (ransomware) $1.9 million
Average ransomware attack total cost $5.13 million
Security investment should be framed around operational risk mitigation and revenue protection, not just data protection. When a security initiative prevents even a single day of production downtime, it pays for itself many times over.
Turning IT/OT Convergence Risk into Competitive Advantage
IT/OT convergence isn’t optional. The economic imperative is too strong—the efficiency gains, the operational visibility, the new business models that real-time industrial data enables. Organizations that refuse to converge will lose to competitors who embrace it.
But convergence without security is a disaster in waiting. With 73% of organizations already experiencing OT breaches, and state-sponsored actors actively pre-positioning for infrastructure disruption, the threat is neither theoretical nor distant.
The organizations that will thrive share these characteristics:
They treat IT/OT security as a board-level priority with clear ownership, adequate budget, and executive accountability—not a technical problem delegated to committees.
They implement defense-in-depth using established frameworks like IEC 62443 and zero trust architectures, recognizing that no single control is sufficient.
They bridge the cultural divide between IT and OT through cross-functional teams, shared metrics, and mutual respect for different operational realities.
They accept that legacy systems require compensating controls rather than waiting for patch cycles that will never come. The 20-year-old PLC can’t be updated, but it can be segmented, monitored, and protected.
They build resilience assuming breach rather than hoping perimeter defenses hold. When—not if—attackers get in, how quickly can you detect them? How effectively can you contain the damage? How fast can you recover?
The $4.5 trillion industrial IoT opportunity comes with proportional risk. Organizations that master IT/OT convergence security won’t just avoid catastrophic losses. They’ll gain competitive advantage through operational confidence, regulatory compliance, and the customer trust that comes from demonstrating they take security seriously.
The collision course is set. Your trajectory from here is a choice.
Published: February 11, 2026
Key Takeaways for IT/OT Security Leaders
- Convergence is inevitable: The majority of industrial organizations have already adopted IT/OT convergence—the question is whether your security program has kept pace with this transformation.
- Quantify your risk: 73% of organizations experienced OT breaches in 2024. Ransomware downtime costs average $1.9 million per day. Use these figures to secure executive buy-in and budget.
- Resolve governance immediately: While 80% of CISOs officially oversee OT, only 35% have mature integrated operations. Assign clear ownership, build cross-functional teams, and fund appropriately.
- Build on segmentation: Implement the Purdue Model architecture and IEC 62443 zones and conduits as your foundation before pursuing advanced zero trust capabilities.
- Apply zero trust to OT: Never trust, always verify—even for internal OT communications. Legacy systems that can’t be patched can still be segmented and monitored.
- Leverage compliance for competitive advantage: IEC 62443, NIST CSF, and NIS2 alignment increasingly determines contract eligibility and customer trust.
- Execute in phases: Assessment in months 1-3, foundation building in months 4-9, maturity advancement in months 10-18. Start now.
About Secure IoT Office
Secure IoT Office provides strategic guidance for organizations navigating the complex intersection of operational technology, cybersecurity, and digital transformation. We help operations leaders build cyber-resilient industrial environments through expert analysis, practical frameworks, and actionable intelligence.
*For more insights on IT/OT convergence security, OT threat landscape analysis, and industrial cybersecurity best practices, subscribe to our newsletter. Visit our sister site for IoT House best practices: *