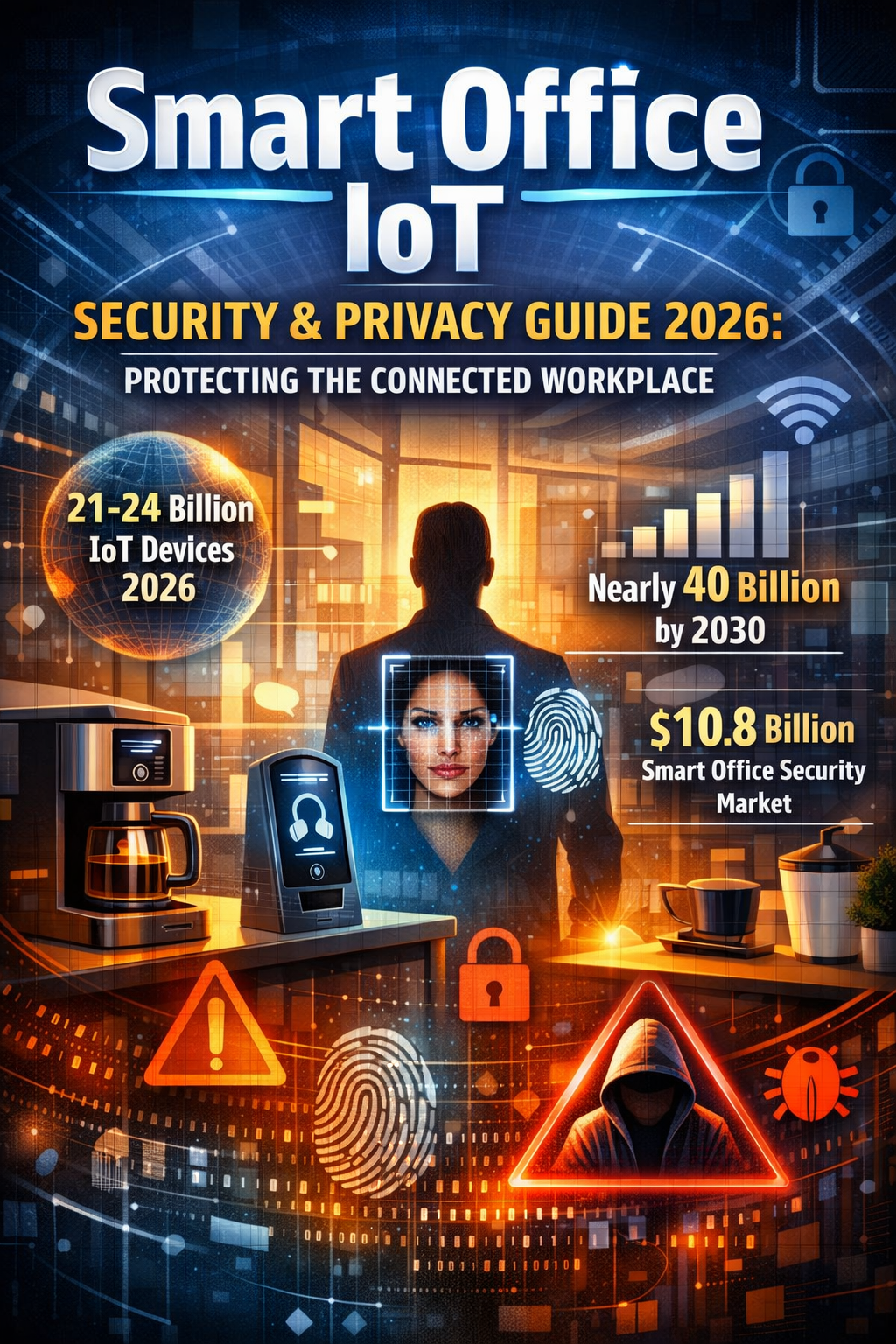
The modern office has transformed into a sophisticated ecosystem of interconnected devices. From smart thermostats and occupancy sensors to facial recognition systems and connected coffee machines, Internet of Things (IoT) devices now permeate every corner of the workplace. While these technologies promise unprecedented efficiency and automation, they also introduce critical security vulnerabilities and privacy concerns that organizations can no longer afford to ignore.
The Smart Office Explosion: Promise and Peril
By 2026, the global IoT landscape has reached a critical inflection point. Current estimates place the number of connected IoT devices between 21-24 billion globally, with projections suggesting nearly 40 billion devices by 2030. The smart office security market alone is expected to reach $10.8 billion by 2033, growing at a compound annual growth rate of 6.3%.
This explosive growth brings both opportunity and risk. Smart offices leverage IoT to:
- Automate HVAC systems based on occupancy and environmental conditions
- Optimize energy consumption through intelligent lighting and climate control
- Enhance security with biometric access control and advanced surveillance
- Streamline inventory management using RFID tracking
- Enable predictive maintenance through continuous equipment monitoring
- Facilitate hybrid work with intelligent scheduling and space utilization tracking
However, this connectivity comes at a cost. Recent analyses reveal a 33% rise in average device risk scores compared to the previous year, with over 50% of IoT devices containing critical vulnerabilities that attackers can exploit immediately.
The 2026 Threat Landscape: What’s Changed
Rising Attack Sophistication
Industrial IoT attacks have increased by 75% in the past two years, with operational technology increasingly targeted through simple automated scans exploiting decades-old, unpatched vulnerabilities. The average IoT security incident now costs businesses $330,000, with regulated industries facing additional fines often reaching millions of dollars.
One particularly alarming trend: one in three data breaches now involves an IoT device, representing a dramatic escalation from previous years.
Real-World Breach Examples
The 2025 Mars Hydro and LG-LED Solutions incident exposed 2.7 billion records, including Wi-Fi credentials and device IDs, demonstrating how misconfigured IoT databases can provide attackers with direct pathways into enterprise networks. Research by Palo Alto Networks confirms that 57% of IoT devices remain highly vulnerable due to outdated operating systems or lack of encryption.
The Convergence of AI and IoT Attacks
Threat actors are increasingly leveraging artificial intelligence to conduct reconnaissance, identify vulnerable devices, and launch polymorphic attacks that evade signature-based detection systems. Shadow AI and autonomous code creation have emerged as legitimate risks, with scripts capable of rewriting themselves and internal agents making access decisions without human awareness.
Critical Vulnerabilities in Smart Office Environments
1. Insecure Design and Default Configurations
The fundamental problem starts with device manufacturers who optimize for cost, time-to-market, and functionality over security. This creates a systemic “insecurity-by-design” phenomenon:
- Default Credentials: 35% of consumer IoT devices still ship with default credentials enabled
- Hard-coded Keys: Approximately 17% of IoT devices contain hard-coded credentials embedded in firmware
- Unencrypted Communication: 24% of IoT companion apps suffer from SSL/TLS issues
- Limited Update Capability: 33% of IoT devices run outdated firmware with no practical update mechanism
2. Lack of Patch Management
Unpatched firmware is responsible for 60% of IoT security breaches. Many devices lack support for updates or receive infrequent patches, leaving known vulnerabilities exposed for extended periods. The challenge is compounded by operational constraints—devices deployed in remote locations or critical infrastructure cannot be easily taken offline for maintenance.
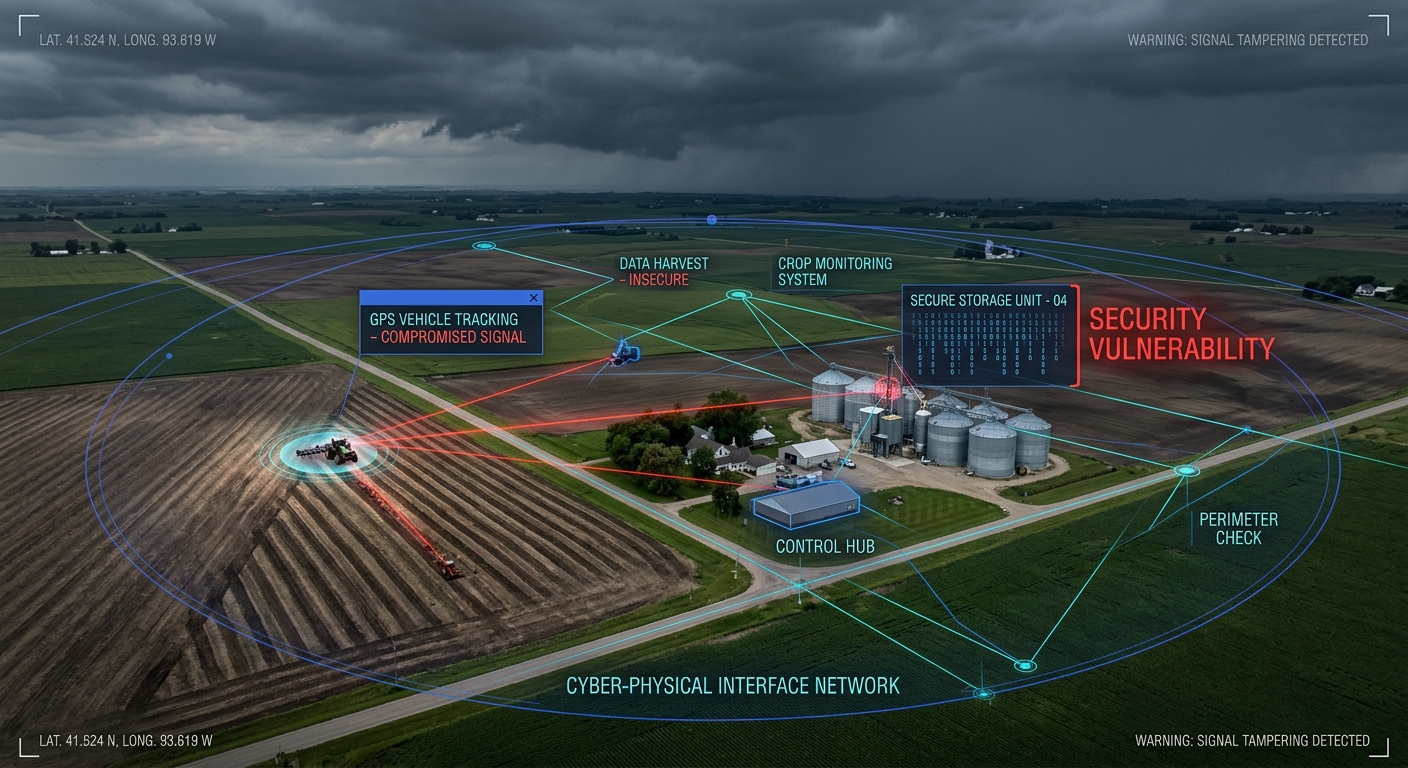
3. Shadow IoT Proliferation
With remote and hybrid work becoming standard, personal IoT devices increasingly coexist on corporate networks. This “shadow IoT” represents one of the fastest-growing enterprise risks, with employees connecting unauthorized smart devices that create unmanaged entry points outside IT’s visibility.
4. Insecure APIs and Cloud Integration
Cloud-control compromises have increased by 38% year-over-year, as weak authentication mechanisms and inadequate rate-limiting on building management APIs enable remote exploitation. IoT devices depend on mobile apps and cloud platforms that often lack secure communication protocols.
5. Network Architecture Weaknesses
Many organizations fail to properly segment IoT devices from critical corporate systems. When a smart thermostat or coffee machine shares network space with servers containing sensitive data, a single compromised device can provide lateral movement opportunities for attackers.
Privacy Implications: The Surveillance Paradox
Beyond security vulnerabilities, smart offices raise profound privacy concerns that organizations must navigate carefully to maintain employee trust and regulatory compliance.
Pervasive Data Collection
IoT devices collect far more information than employees realize. For example:
- Environmental Sensors: A simple CO2 monitor can reveal room occupancy, number of people present, general activities (meetings, eating), and arrival/departure times
- Occupancy Sensors: Track employee movements, workspace utilization patterns, and behavioral habits
- Smart Cameras and Audio: Continuously capture visual and audio data, creating permanent records of workplace interactions
- Biometric Systems: Collect and store sensitive personal identifiers like fingerprints, facial geometry, or iris scans
- Wearable Devices: Monitor health metrics, location data, and activity patterns
Research shows that while employees are aware of some data collection, they lack confidence in understanding what is collected and how it’s used. Most concerning: as multiple data sources are fused together, the potential for revealing inferences grows exponentially.
Consent and Transparency Gaps
Employee consent is often implicit rather than explicit. Insufficient transparency about data collection, usage, and access erodes trust and morale. Studies indicate that employees accept some monitoring at work but express significant concern about data inferences that could reveal personal information—particularly when those in positions of authority might use data against subordinates.
Third-Party Access Risks
Vendors managing IoT platforms may have visibility into sensitive data, raising concerns about how information is used, shared, and secured externally. Cheap network cameras and IoT devices frequently transmit data overseas for unclear purposes, potentially including espionage, advertising, or worse—ending up in publicly accessible cloud storage buckets.
Regulatory Compliance Challenges
Organizations face a complex web of privacy regulations:
- GDPR: Requires transparent handling of personal data and empowers individuals with rights over their information
- CCPA/CPRA: Grants California residents control over their data with penalties up to $7,988 per intentional violation (doubled for minors’ data)
- HIPAA: Connected medical devices transmitting patient data fall under protected health information safeguards
- State-Level Regulations: Virginia, Colorado, Connecticut, and other states have enacted comprehensive privacy laws
The California Privacy Protection Agency now handles audits, rulemaking, and investigations with businesses no longer receiving automatic 30-day cure periods for violations.
Building a Comprehensive IoT Security Framework
Securing smart offices requires a multi-layered approach combining technical controls, governance frameworks, and organizational processes.
1. Asset Discovery and Inventory Management
Every organization should know what IoT and OT devices are connected on its networks, where they connect, and what privileges they possess.
- Implement continuous device discovery systems
- Maintain real-time asset inventories
- Document device types, locations, firmware versions, and communication patterns
- Track vendor relationships and support lifecycles
In August 2025, CISA joined eight international agencies to declare OT asset inventory a foundational Cybersecurity Performance Goal, marking a pivotal shift in critical infrastructure security requirements.
2. Network Segmentation and Zero Trust Architecture
Network segmentation and zero trust are non-negotiable for modern smart office security:
- Operational Network: Dedicated segment for building management systems, HVAC, and security cameras
- Corporate Network: Employee devices and sensitive data systems
- Guest Network: Complete isolation of visitors from critical infrastructure
- VLANs: Micro-segmentation for IoT device categories (smart lights, printers, sensors) to limit lateral movement
Implement strict access controls that:
- Verify device identity before network access
- Apply least privilege principles
- Enforce continuous authentication and authorization
- Monitor for anomalous behavior patterns
3. Secure Development and Procurement Standards
Organizations must demand security by design from vendors:
- Secure Boot: Verify firmware integrity before execution
- Code Signing: Ensure updates come from legitimate sources
- Over-the-Air Updates: Built-in, verifiable update mechanisms
- Cryptographic Standards: Modern encryption algorithms with upgrade paths
- Hardware Security: Trusted Platform Modules (TPMs) or Hardware Security Modules (HSMs)
Critical Procurement Requirement: Devices that cannot be patched securely should not be deployed in business environments. Period.
4. Identity and Access Management
Move from perimeter-based to identity and behavior-based defense:
- Change Default Credentials: Create unique, complex passwords for every IoT device immediately upon deployment
- Multi-Factor Authentication: Implement MFA for all device administration interfaces
- Privileged Access Management: Strictly control who can install, configure, and monitor IoT devices
- Service Account Governance: Establish inventories of non-human actors and baseline their behavior
5. Data Protection and Privacy Controls
Data Minimization: Collect and process only the minimum data necessary for intended functions, reducing privacy risks and exposure from potential breaches.
- Encryption at Rest: Protect stored data with strong algorithms and secure key management
- Encryption in Transit: Use TLS/SSL for all device-to-cloud communications
- Data Classification: Categorize IoT data based on sensitivity and regulatory requirements
- Privacy by Design: Embed privacy considerations throughout system design
- Access Controls: Define clear policies for who can access what data and when
- Data Retention: Implement appropriate retention schedules and secure deletion procedures
6. Firmware and Patch Management
Establish rigorous update processes:
- Automated Update Schedules: Enable automatic security patches where possible
- Testing Protocols: Validate updates in non-production environments before deployment
- Rollback Procedures: Maintain ability to revert problematic updates
- End-of-Life Planning: Replace devices that no longer receive manufacturer support
7. Continuous Monitoring and Threat Detection
Deploy behavioral analytics to identify anomalies:
- Traffic Analysis: Monitor unusual communication patterns from IoT devices
- Baseline Establishment: Define normal device behavior to detect deviations
- SIEM Integration: Centralize IoT event data for correlation and analysis
- AI-Powered Detection: Leverage machine learning for real-time anomaly detection
- Incident Response: Establish clear procedures for IoT security events
Organizations report average downtime of 6.5 hours per IoT cyberattack—preparation and monitoring can dramatically reduce this impact.
8. Physical Security Integration
Remember that IoT devices exist in physical space:
- Tamper Detection: Implement mechanisms to alert on physical device access
- Secure Enclosures: Protect devices from unauthorized physical manipulation
- Environmental Monitoring: Track conditions that might affect device security
- Access Controls: Restrict physical access to critical IoT infrastructure
Governance and Organizational Framework
Technical controls alone are insufficient. Organizations need comprehensive governance:
Security Policy Development
Create explicit policies governing:
- Installation Procedures: Standard processes for device onboarding
- Configuration Baselines: Secure configuration templates for common device types
- Acceptable Use: Clear guidelines on permitted IoT devices and applications
- BYOD Policies: Specific controls for personal IoT devices in workplace environments
- Decommissioning: Secure procedures for removing devices from service
Employee Training and Awareness
Transform employees from potential weak links to proactive defenders:
- Security Awareness: Regular training on IoT threats and best practices
- Privacy Education: Help employees understand data collection and their rights
- Incident Reporting: Encourage reporting of suspicious device behavior
- Role-Specific Training: Targeted education for administrators and power users
According to TrustArc’s 2025 Benchmarks Report, 71% of organizations now provide broad training across roles, moving beyond mere compliance to raise awareness of evolving risks including AI misuse and IoT vulnerabilities.
Vendor Risk Management
Scrutinize third-party IoT providers:
- Security Certifications: Require SOC 2, ISO 27001, or equivalent documentation
- Contractual Obligations: Include security requirements and incident notification clauses
- Regular Assessments: Conduct periodic security reviews of vendor products
- Data Handling Agreements: Clearly define vendor access to and use of collected data
Organizations should audit vendors before signing contracts and treat vendor risk management with the same scrutiny as internal environments.
Compliance Framework Integration
Align IoT security with regulatory requirements:
- NIST Cybersecurity Framework: Implement identification, protection, detection, response, and recovery controls
- ISO/IEC 27001: Apply information security management principles to IoT environments
- CMMC: Defense contractors must ensure adequate cybersecurity practices for DoD work
- Industry-Specific Standards: Healthcare (HIPAA), financial services (PCI DSS), and other sector requirements
Emerging Technologies and Future Considerations
AI-Driven Security
Artificial intelligence is strengthening IoT security through:
- Real-time Anomaly Detection: Identify unusual patterns before they cause harm
- Predictive Threat Analysis: Anticipate potential attacks based on behavioral patterns
- Automated Response: Reduce time to contain cyberattacks through intelligent automation
The IoT security market, driven by AI integration, is projected to grow from $24.2 billion in 2024 to $56.2 billion by 2029, reflecting an 18.4% compound annual growth rate.
Quantum Computing Preparations
Organizations are increasingly advocating for early adoption of quantum-resistant security solutions:
- Tokenization: Implement quantum-safe cryptographic methods
- Algorithm Agility: Design systems capable of transitioning to post-quantum cryptography
- Long-Term Data Protection: Protect data before quantum threats materialize
5G and Edge Computing
The rollout of 5G networks and edge computing architectures introduces new security paradigms:
- Increased Device Density: More devices per square foot requiring management
- Edge Processing: Security controls must extend to edge computing nodes
- Network Slicing: Requires sophisticated segmentation and isolation techniques
Regulatory Evolution
New frameworks continue to emerge:
- US Cyber Trust Mark: Helps consumers identify IoT devices meeting specific cybersecurity standards
- EU Cyber Resilience Act: Mandates cybersecurity requirements for all IoT devices in European markets
- Privacy Act Modernization: Proposed US federal legislation to strengthen data protection rights
Practical Implementation Roadmap
Phase 1: Foundation (Months 1-3)
- Conduct comprehensive IoT device inventory
- Assess current security posture and identify critical gaps
- Develop security policies and governance framework
- Implement basic network segmentation
- Change all default credentials
Phase 2: Enhancement (Months 4-6)
- Deploy continuous monitoring and asset discovery systems
- Establish automated patch management processes
- Implement behavioral analytics and anomaly detection
- Conduct employee security awareness training
- Begin vendor risk management program
Phase 3: Optimization (Months 7-12)
- Deploy advanced threat detection and response capabilities
- Integrate IoT security with enterprise SIEM/SOAR platforms
- Implement privacy-enhancing technologies
- Conduct regular penetration testing and vulnerability assessments
- Establish metrics and continuous improvement processes
Smart Office Security Checklist
Device Level:
- Change default passwords to unique, complex credentials
- Enable automatic firmware updates where available
- Disable unnecessary features and services
- Implement secure boot and code signing
- Configure encryption for data at rest and in transit
Network Level:
- Segment IoT devices from corporate systems
- Implement VLANs for device categories
- Deploy network access control (NAC)
- Configure firewall rules for IoT traffic
- Enable network monitoring and logging
Organizational Level:
- Maintain current device inventory
- Document data flows and privacy implications
- Establish incident response procedures
- Conduct regular security training
- Review vendor security postures
- Ensure regulatory compliance
- Test business continuity plans
Privacy Level:
- Conduct privacy impact assessments
- Provide transparent privacy notices
- Establish data minimization practices
- Implement data subject rights processes
- Define clear data retention policies
- Secure third-party data processing agreements
Conclusion: Security as a Strategic Imperative
The smart office revolution is irreversible. IoT devices will continue proliferating, and their integration into workplace operations will only deepen. Organizations that treat IoT security as an afterthought—or worse, ignore it entirely—face existential risks ranging from devastating data breaches to regulatory fines, operational disruption, and reputational damage.
Research shows that 78% of consumers would stop using a company’s services after a major IoT-related breach. In the B2B context, a single security incident can terminate client relationships, destroy years of trust-building, and result in catastrophic financial losses.
Conversely, organizations that embed security and privacy into their smart office deployments gain competitive advantages:
- Enhanced Trust: Employees and customers confidence in data protection
- Regulatory Compliance: Avoiding fines and legal exposure
- Operational Resilience: Reduced downtime and faster incident recovery
- Innovation Enablement: Secure foundation for deploying emerging technologies
The fundamental challenge of 2026 is clear: combine secure engineering, smarter procurement, stronger compliance frameworks, and a workforce prepared for the hybrid world where physical systems meet software. Organizations that invest deliberately in IoT security—technically, organizationally, and strategically—will transform connectivity from a sprawling vulnerability into a foundation of resilient, efficient operations.
The connected workplace is here. The only question is whether organizations will secure it before adversaries exploit it.
Additional Resources
Frameworks and Standards:
- NIST Cybersecurity Framework: https://www.nist.gov/cyberframework
- IoT Security Foundation Compliance Framework: https://iotsecurityfoundation.org
- ISO/IEC 27001 Information Security Management
- Industrial Internet Consortium Security Framework
Regulatory Guidance:
- CISA IoT Security Resources: https://www.cisa.gov
- EU Cyber Resilience Act Implementation
- FTC IoT Security Guidance
- State Privacy Law Compliance Resources
Industry Reports:
- Forescout 2025 Device Risk Report
- Verizon Data Breach Investigations Report
- Palo Alto Networks IoT Threat Report
- ONEKEY OT & IoT Cybersecurity Report
Tools and Solutions:
- Network Access Control (NAC) platforms
- IoT-specific SIEM integration modules
- Automated vulnerability scanning tools
- Device discovery and inventory systems
- Privacy impact assessment frameworks
Last Updated: December 2025