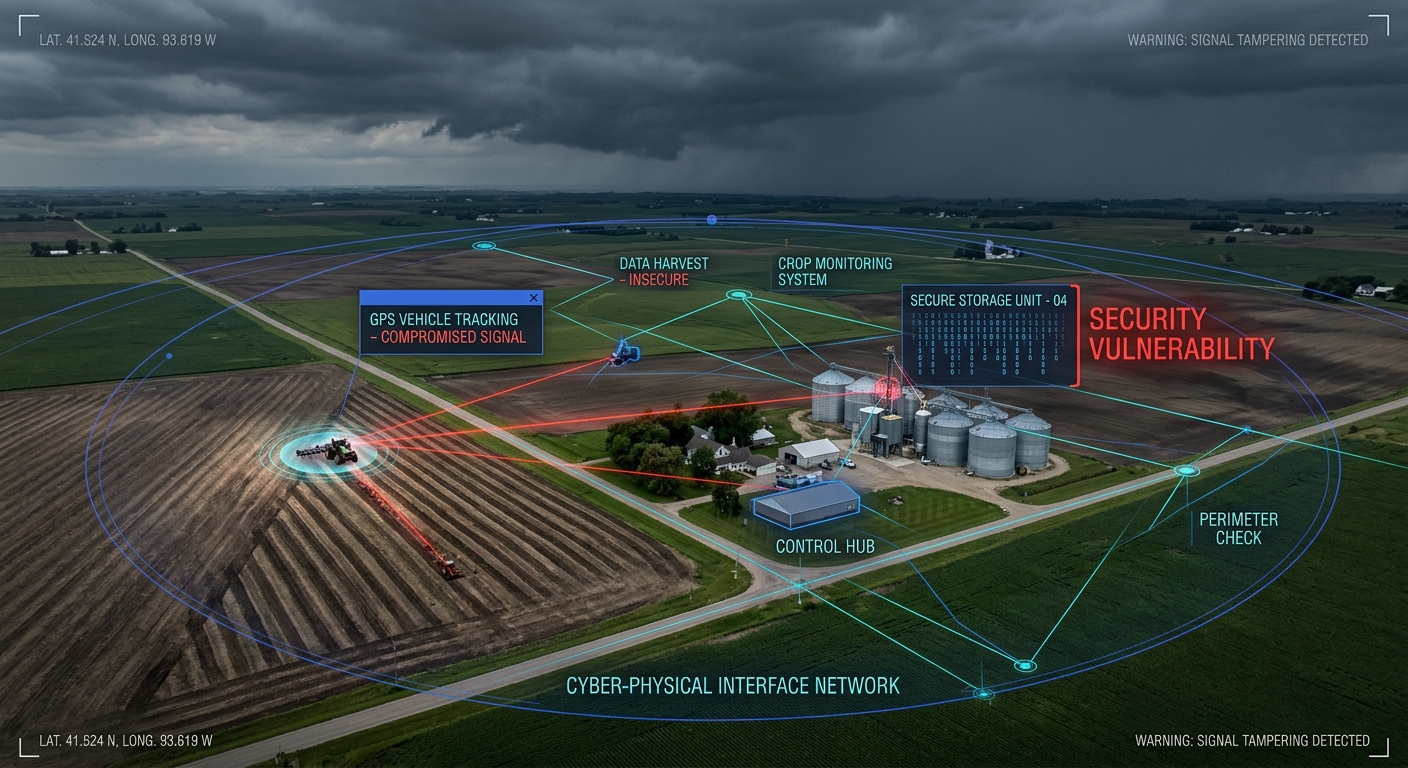
Your smart building systems—HVAC controllers, security cameras, access badges, and lighting systems—are all IoT devices. And in too many enterprises, they share network infrastructure with critical business systems. This is a ticking time bomb.
Why IoT Devices Are Different
Enterprise IoT devices present unique security challenges:
- Limited patching capability — Many run embedded firmware that’s rarely updated
- Weak authentication — Default credentials are disturbingly common
- Long lifecycles — That HVAC controller might run for 15+ years
- Physical accessibility — Devices in hallways and ceilings can be tampered with
- Vendor dependencies — Third-party maintenance often requires network access
When an attacker compromises a smart thermostat, they shouldn’t be able to pivot to your ERP system. Network segmentation prevents this.
Segmentation Architecture
Tier 1: Critical Business Systems
Your ERP, financial systems, HR databases, and intellectual property live here. Zero IoT devices should have any path to this segment.
- Strict firewall rules
- No inbound connections from lower tiers
- Comprehensive logging and monitoring
Tier 2: Corporate User Network
Standard employee workstations and laptops. Limited, audited connections to Tier 1.
- NAC (Network Access Control) enforcement
- Endpoint detection and response
- Standard corporate security policies
Tier 3: IoT Device Networks
Further segment by function and risk:
3A: Building Management Systems (BMS)
- HVAC, lighting, elevator controls
- Air-gapped from internet where possible
- Vendor access via jump boxes only
3B: Physical Security Systems
- Cameras, access control, intrusion detection
- Separate from BMS to prevent cross-compromise
- Dedicated management VLAN
3C: Guest/Visitor IoT
- Conference room displays, visitor WiFi
- Heavily restricted, internet-only access
- No path to internal resources
Tier 4: Vendor/Maintenance Access
Controlled jump boxes for third-party access:
- Time-limited access windows
- Full session recording
- MFA required
Implementation Considerations
VLANs Are Necessary But Not Sufficient
VLANs provide logical separation, but without proper ACLs and firewall rules, traffic can still traverse segments. Implement:
- Inter-VLAN routing restrictions
- Micro-segmentation where possible
- East-west traffic monitoring
DNS and DHCP Isolation
IoT devices often use DNS for command-and-control callbacks. Segment DNS:
- Dedicated DNS servers per segment
- DNS query logging and analysis
- Block external DNS for IoT segments (force internal resolution)
Consider Zero Trust Network Access (ZTNA)
Modern ZTNA solutions can enforce identity-based segmentation regardless of network location:
- Device posture checks before access
- Continuous authentication
- Application-layer segmentation
Compliance Alignment
Proper IoT segmentation helps satisfy multiple compliance frameworks:
- PCI DSS — Requirement 1 (network segmentation to reduce scope)
- HIPAA — Technical safeguards for ePHI
- SOC 2 — Logical and physical access controls
- NIST CSF — Protect function, network integrity
Document your segmentation architecture—auditors will ask for it.
Common Pitfalls
- Flat networks with VLAN tagging only — VLANs without ACLs are security theater
- Allowing IoT-to-internet without inspection — Command-and-control traffic goes undetected
- Shared credentials across segments — One compromise unlocks everything
- Forgetting about IPv6 — Your segmentation might only apply to IPv4
- No asset inventory — You can’t segment what you don’t know exists
Getting Started
If you’re starting from a flat network:
- Inventory all IoT devices — You’ll find more than you expect
- Map communication patterns — Understand what talks to what
- Design target architecture — Plan your segments
- Implement incrementally — Start with highest-risk devices
- Monitor and adjust — Segmentation is ongoing, not one-time
Your IoT devices will only multiply. Build the segmentation foundation now, before the next smart coffee maker becomes your breach point.