Start with the numbers, because they are genuinely staggering.
Between 2019 and 2022, researchers and journalists catalogued over 40 food processing facilities across the United States that experienced fires, explosions, or other destructive events severe enough to disrupt operations. Egg farms and poultry facilities reported losses of hundreds of thousands of birds in fires at facilities in Iowa, Connecticut, South Carolina, and elsewhere — events attributed primarily to equipment failures and accidents, but occurring at a pace that drew uncomfortable attention. Grain silo fires, long a routine agricultural hazard, appeared to be accelerating in frequency. Farm report aggregators tracking incidents across ranches, processing plants, and grain storage operations identified patterns that, when assembled, suggested a sector under unusual stress.
If you add up the documented incidents — fires, equipment failures, cyberattacks, “unexplained” operational disruptions — across U.S. farms, ranches, food processing facilities, and agriculture-adjacent infrastructure over the past five years, the cumulative figure runs into the thousands. The exact count depends heavily on how you define “incident” and how rigorously you document events that rural operators rarely publicize. But the trajectory is clear: something is happening to America’s food infrastructure, and the cybersecurity community has been almost entirely absent from the conversation.
This is not a conspiracy theory piece. The documented cyber-physical attack surface in modern American agriculture is real, serious, and almost entirely undefended. This is that analysis.
The Documented Cyber Incidents: What We Know Happened
Before addressing the broader patterns, let’s establish the confirmed cyberattacks — incidents where digital intrusions directly impacted the food supply chain.
JBS Foods, May 2021. The world’s largest meat processing company was struck by REvil ransomware, forcing the closure of five beef processing plants in the United States for three days. JBS ultimately paid $11 million in ransom to recover its systems. The attack briefly removed approximately 25% of U.S. beef processing capacity from the market, driving meat prices higher and exposing how concentrated and fragile the food processing supply chain had become. The FBI attributed the attack to REvil, a Russian-linked ransomware-as-a-service group.
Crystal Valley Cooperative, September 2021. A Minnesota farm supply and grain marketing cooperative was hit by ransomware just two weeks after JBS, disrupting fuel delivery, grain delivery acceptance, and financial operations at a critical point in the harvest season. The timing was not accidental — ransomware operators understand agricultural seasonality and deliberately attack during planting and harvest windows when the cost of downtime is maximized.
NEW Cooperative, September 2021. An Iowa grain cooperative serving approximately 40% of the U.S. grain supply network was breached by BlackMatter ransomware. The group demanded $5.9 million, explicitly claiming they had SCADA and agricultural systems access. CISA issued warnings that the attack could affect grain storage and transport operations.
UNFI (United Natural Foods), October 2022. The Empty Shelves incident: UNFI, which supplies approximately 30,000 store locations including Whole Foods and regional grocers, suffered a cyberattack that disrupted distribution operations. Retailers reported inventory shortfalls and empty shelves as the company worked to restore systems. UNFI is a critical link in the organic and natural food supply chain — a single attack on this intermediary cascaded across thousands of retail locations.
EBT System Breach, October 2023. In what represented a direct attack on the social safety net for food security, the California EBT (Electronic Benefits Transfer) system — which delivers SNAP food stamp benefits — was hit by skimming attacks that drained accounts for thousands of low-income families. Similar attacks hit EBT systems in multiple states. While technically different from agricultural infrastructure attacks, these incidents demonstrated that adversaries are willing to attack every layer of the food supply system, from production to distribution to consumption.
Dole PLC, February 2023. The global produce giant suffered a ransomware attack that disrupted North American operations, caused temporary food shortages at some U.S. grocery stores, and forced Dole to shut down production facilities. The incident revealed that even diversified global food companies with substantial IT resources are vulnerable.
This is the confirmed public record. Security researchers and law enforcement believe the actual attack count is significantly higher — most agricultural cooperatives and food processors do not publicly disclose incidents, and many lack the detection capability to even know they’ve been breached.
The Physical Incident Acceleration: What the Data Shows
The cyber incidents are the clearest part of the picture. The physical incident pattern is more complex and requires careful treatment.
Food processing plant fires (2019-2022): Multiple researchers and journalists documented what appeared to be an unusual cluster of fires, explosions, and other incidents at U.S. food processing facilities during this period. The National Fire Protection Association, when asked in 2022, stated that the data “does not signal anything out of the ordinary” compared to historical baselines. Food processing plants are inherently high-risk environments — cooking oils, grain dust, refrigerants, and industrial equipment create fire hazards that require constant management.
What security researchers note, however, is that the pattern of what was affected matters as much as the frequency. Several of the highest-profile incidents between 2019-2022 affected protein processing (beef, poultry, pork) — precisely the segment of the food supply chain that JBS and other ransomware victims were targeting digitally. Whether this represents correlation, coincidence, or something more intentional remains an open question that neither CISA nor the FBI has publicly addressed.
Poultry facility fires: The destruction of hundreds of thousands of chickens and turkeys in facility fires — many attributed to standard agricultural equipment failures — drew scrutiny in 2021-2022, particularly given the concurrent avian influenza outbreaks that were forcing culls of millions of birds. Security analysts noted that the combination of physical fires, disease-driven culls, and digital attacks on meat processors created simultaneous pressure across multiple points in the protein supply chain.
Grain storage incidents: Grain silo fires and explosions are an endemic agricultural hazard — grain dust is explosive under the right conditions, and silos create confined environments where ignition risks are elevated. The documented acceleration in grain storage incidents during 2021-2022 remains ambiguous: some attribute it to increased grain storage volumes, deferred maintenance during COVID, and operator fatigue. The more concerning possibility — that grain storage infrastructure was being specifically targeted as a food supply disruption vector — has not been established with public evidence.
The security-relevant takeaway is not that all these incidents were coordinated attacks. It’s that a sophisticated adversary looking to disrupt U.S. food security would not need to coordinate all of them — they would only need to amplify existing vulnerabilities and create a few well-timed disruptions at critical chokepoints.
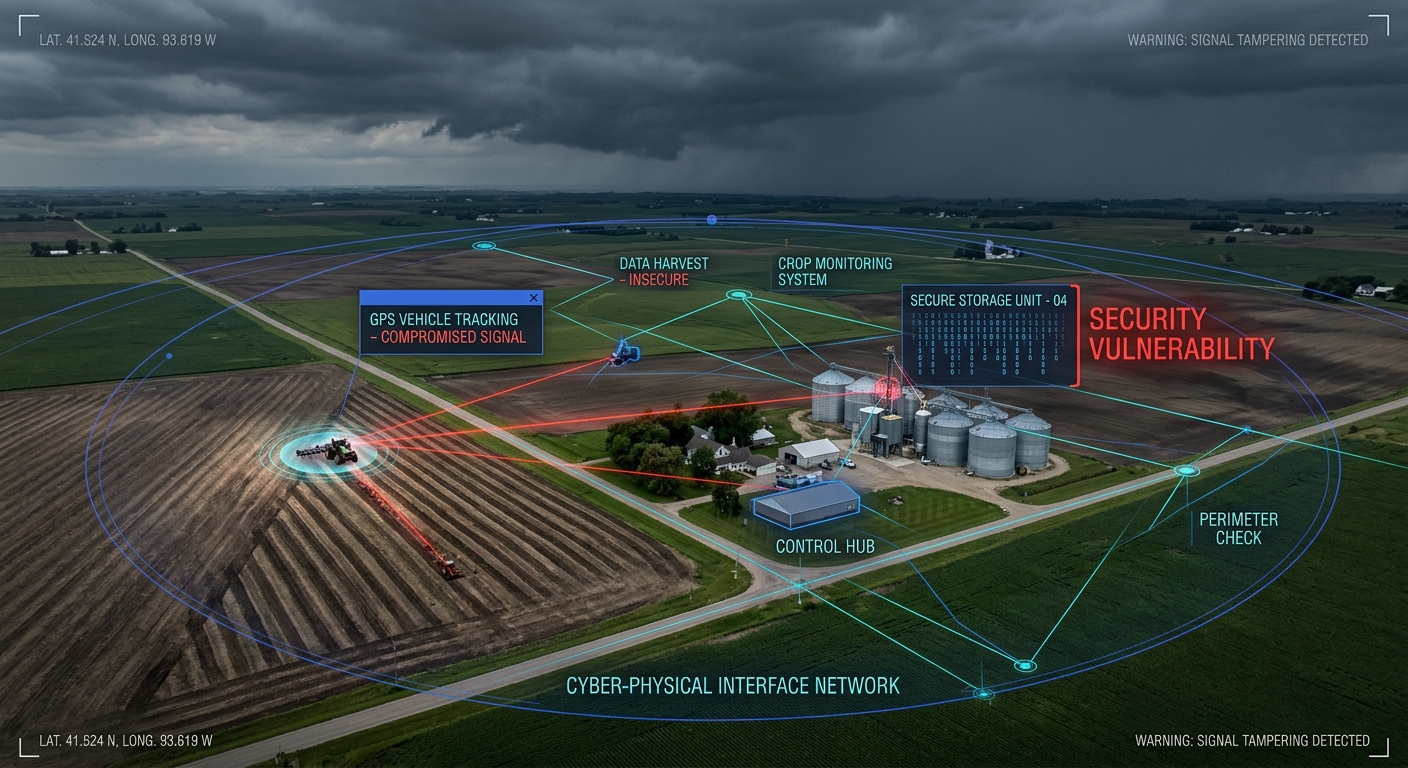
The Cyber-Physical Attack Surface: Modern Agriculture Is Not What It Was
Here is where the security analysis becomes genuinely alarming.
American agriculture in 2026 is not the analog, weather-dependent enterprise of previous generations. It is a deeply networked, data-driven, software-dependent industry — and most of the security community has no idea.
John Deere and precision agriculture: Modern John Deere tractors are essentially software-defined vehicles operating on GPS guidance systems, connected to the John Deere Operations Center cloud platform. A single tractor can generate gigabytes of planting, yield, and soil composition data per day. The Operations Center platform allows remote diagnostics, software updates, and in some cases remote operation. In 2022, security researchers demonstrated critical vulnerabilities in John Deere’s systems that could have allowed attackers to remotely take over equipment. While John Deere patched the disclosed vulnerabilities, the fundamental attack surface — network-connected, GPS-guided, software-dependent farm equipment — remains.
In 2024, CISA issued warnings that foreign-manufactured agricultural drones used for crop monitoring and pesticide application posed “serious threats to critical infrastructure,” noting they could be turned off, rerouted, or weaponized as instruments of geopolitical pressure. A fleet of pesticide-delivery drones with compromised firmware doesn’t just fail to apply pesticides — it could apply them incorrectly, in wrong concentrations, or to wrong fields.
Irrigation as SCADA infrastructure: Large-scale irrigation in the American West and agricultural heartland is almost entirely SCADA-controlled. Automated pivots, pump stations, valve systems, and soil moisture sensors feed into control systems that manage water application across thousands of acres. Many of these systems use cellular or radio connectivity with minimal authentication. A 2021 incident in Oldsmar, Florida — where an attacker accessed a water treatment plant’s SCADA system and attempted to dramatically increase sodium hydroxide levels — demonstrated exactly how accessible these systems are to remote attackers. The same attack pattern applied to irrigation systems could devastate crop cycles by flooding fields, withholding water during critical growth windows, or introducing contaminants.
Automated feedlots: Large-scale cattle and hog feeding operations rely on automated feed delivery, water systems, and climate control in confined animal feeding operations (CAFOs). These systems are typically managed by dedicated PLCs and HMIs connected to operations management software. An attacker who compromises feedlot control systems could manipulate feed timing and composition (affecting animal health and growth), disable water systems, or interfere with waste management — any of which could result in mass animal losses and significant environmental consequences.
Cold chain logistics: The cold chain — refrigerated transport and storage that keeps perishable food safe between harvest and consumption — runs on networked temperature monitoring, automated refrigeration systems, and logistics management software. A targeted attack on cold chain infrastructure could spoil large volumes of food invisibly — by subtly elevating temperatures outside safe ranges while falsifying monitoring data, for example. This type of attack would be extremely difficult to detect before the damage was done.
IoT sensor networks: Precision agriculture relies on dense networks of IoT sensors monitoring soil conditions, weather, crop health, and equipment status. These sensors typically have minimal security controls, long operational lifespans, and limited update mechanisms. Compromised sensors could feed false data into farm management systems, leading to incorrect planting, irrigation, fertilization, or pesticide decisions.
What a State-Actor Food Supply Disruption Campaign Would Look Like
A sophisticated state-level adversary targeting U.S. food security would not necessarily launch visible, attributable cyberattacks. The most dangerous scenario is a slow, patient, multi-vector campaign:
Phase 1 — Pre-positioning: Establish persistent access to agricultural SCADA systems, cold chain networks, major food processor IT environments, and agricultural supply chain logistics platforms. This access is maintained dormant, avoiding detection.
Phase 2 — Intelligence collection: Map the dependency relationships between major food processors, distribution networks, retail supply chains, and government food assistance programs. Identify chokepoints — facilities or systems whose disruption would create cascading shortages.
Phase 3 — Activation: In a geopolitical crisis, activate disruptions across multiple vectors simultaneously — ransomware deployed against 2-3 major food processors, physical disruption of key distribution infrastructure, subtle manipulation of cold chain data, and EBT system disruption to maximize civilian impact and erode public confidence in food security.
This isn’t speculative fiction. It’s a documented playbook that mirrors Russian information operations, Chinese infrastructure pre-positioning (documented by CISA and FBI in multiple advisories), and the hybrid warfare doctrine applied to critical infrastructure. Agriculture is explicitly listed as one of 16 critical infrastructure sectors by CISA — but it receives a fraction of the security resources directed at energy, finance, or defense.
What CISOs and Farm Operators Must Do
The security response to agricultural cyber-physical risk is underdeveloped relative to the threat. Here’s a prioritized framework:
For large food processors and agricultural enterprises:
- Implement OT/IT segmentation for all production, processing, and storage control systems. Apply the same rigor you would to any industrial OT environment.
- Deploy SCADA-aware monitoring that can detect anomalous commands, unauthorized access, and configuration changes in agricultural control systems.
- Conduct supply chain cybersecurity assessments — your third-party agricultural technology vendors, logistics providers, and cooperative partners are part of your attack surface.
- Test cold chain integrity systems — verify that temperature monitoring data is authenticated and cannot be falsified without detection.
For agricultural cooperatives and mid-market operators:
- Segment operational networks from business/internet-connected networks. Use firewalls between your farm management software and your field sensors or equipment control systems.
- Change default credentials on all connected equipment — John Deere Operations Center accounts, irrigation controllers, weather stations, and grain management systems.
- Enable multi-factor authentication on all cloud-connected agricultural platforms.
- Maintain offline backups of critical operational data — planting records, yield maps, equipment configurations, and financial records.
- Join ISAC information sharing programs — the Food and Agriculture ISAC (Food and Ag-ISAC) provides sector-specific threat intelligence.
At the policy level: Agricultural cybersecurity requires the same mandatory reporting, minimum security standards, and federal resource support that financial services and energy sectors have developed over the past decade. CISA’s Food and Agriculture Sector risk assessments are informative but not binding. The sector needs clear minimum standards for connected agricultural equipment, cold chain monitoring security, and cooperative network hygiene.
The Uncomfortable Conclusion
The 3,000-incident figure encompasses confirmed cyberattacks, suspected digital intrusions, physical fires and explosions at food infrastructure, and operational disruptions across the agricultural supply chain. Some of these are accidents. Some are criminal ransomware operations motivated purely by profit. Some may be something more.
What is not ambiguous is the attack surface that exists. Modern American agriculture runs on GPS-guided equipment, SCADA-controlled irrigation, networked feedlots, cloud-connected precision agriculture platforms, and a cold chain that depends on networked monitoring. Every one of these systems is connected. Very few of them are secured.
The food supply is the most fundamental critical infrastructure the United States has. Disrupting it doesn’t require attacking military systems or financial markets — it requires patience, access to widely available attack tools, and an understanding of where the chokepoints are.
The chokepoints exist. The question is whether the security community — and the agricultural industry — will take them seriously before they’re exploited at scale.
For guidance on securing IoT and OT systems in critical infrastructure environments, visit Secure IoT Office.
Sources: FBI advisory on JBS ransomware attack (2021); CISA advisory on food and agriculture sector ransomware (2021); Claroty JBS attack analysis; Small Wars Journal “Cyber to Soil” analysis (2025); CISA agricultural drone advisory (2024); High Plains Journal agricultural IoT security analysis (2025); FactCheck.org food plant fire analysis (2022); Food Safety magazine food sector cyber threats (2023).