There is no exotic zero-day in this story. No nation-state malware toolkit with a cinematic name. No months-long patient intrusion that required a team of elite hackers.
What CISA advisory AA26-097A, published this morning by six federal agencies, describes is something more unsettling: Iranian-affiliated hackers walking into US water and energy infrastructure through the front door — because the front door was left unlocked.
The joint advisory, issued by the FBI, CISA, NSA, EPA, the Department of Energy, and US Cyber Command, confirms that the threat group operating under the persona CyberAv3ngers — linked to Iran’s Islamic Revolutionary Guard Corps Cyber Electronic Command (IRGC-CEC) — has been actively targeting internet-exposed Rockwell Automation Allen-Bradley programmable logic controllers across critical infrastructure sectors since at least March 2026. The attacks have caused operational disruptions and financial losses at multiple victim organizations.
This is not a theoretical threat. People lost access to water.
What Happened, and How
The technique the IRGC-linked group used is almost embarrassingly simple, which is precisely what makes it so dangerous.
Rockwell Automation’s Studio 5000 Logix Designer is legitimate industrial software used by engineers to program, configure, and monitor Allen-Bradley PLCs. It’s the tool that legitimate operators use every day to manage production lines, water treatment processes, and power distribution equipment.
The attackers didn’t compromise Studio 5000. They didn’t exploit a vulnerability in it. They simply used it as it was designed to be used — to connect to PLCs that had been inadvertently exposed to the public internet, on devices where authentication controls were either absent or configured with default credentials that no one had changed.
Once connected, the threat actors were able to:
- Read and modify PLC project files — the logic that controls physical processes
- Manipulate data displayed on HMI and SCADA screens — causing operators to see false readings
- Alter operational setpoints — changing the parameters that govern physical systems like pumps, valves, and chemical dosing equipment
- In some cases, cause operational disruption — meaning physical processes were interrupted
The CISA advisory specifically notes disruptions at a water utility in Ireland (where residents lost water service for two days), a water utility in Pennsylvania, and other water facilities in the United States. Energy sector infrastructure and government facilities were also targeted.
The Threat Actor: CyberAv3ngers and the IRGC-CEC
CyberAv3ngers is not a new name in critical infrastructure threat intelligence. The group, also tracked under aliases including Shahid Kaveh Group, Hydro Kitten, Storm-0784, and UNC5691, has been conducting operations against Western and Israeli critical infrastructure since at least 2020.
The group operates under the direction of the IRGC-CEC — a branch of the Islamic Revolutionary Guard Corps with a specific mandate for offensive cyber operations. The IRGC-CEC is distinct from other Iranian APT groups in its explicit focus on operational technology and industrial control systems, rather than espionage or financial theft.
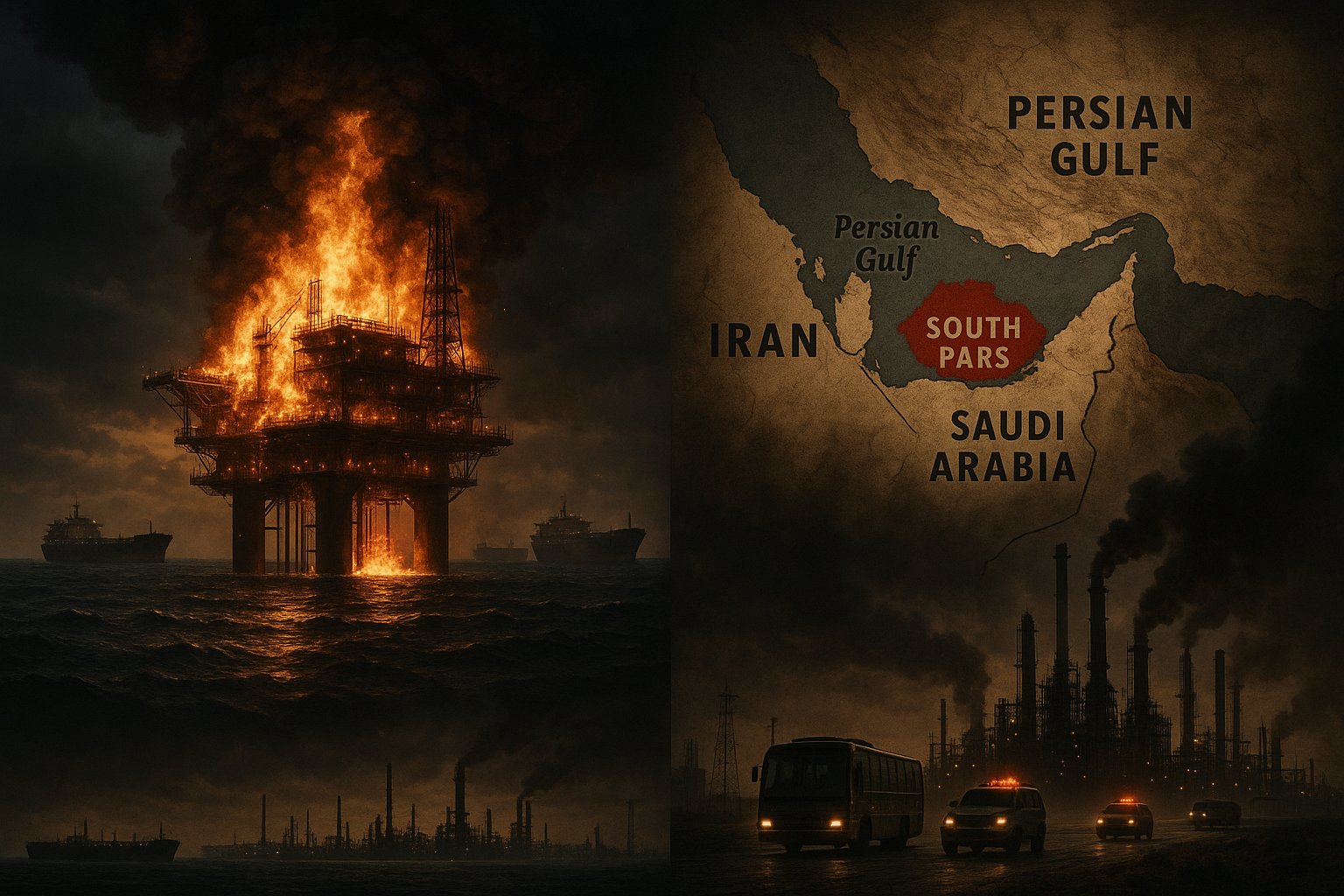
What’s changed in 2026 is the geopolitical context. As the conflict in the Middle East has intensified — with direct strikes on Iranian energy infrastructure, including the South Pars gas field — Iranian state-sponsored groups have escalated operations against Western critical infrastructure. CyberAv3ngers is the sharpest edge of that escalation.
The April 7 advisory marks the most serious public attribution of IRGC-linked attacks on US infrastructure to date. Six federal agencies co-signing a single advisory is not a routine occurrence. It signals that the government assesses this threat as both credible and ongoing.
Why Rockwell Allen-Bradley PLCs?
Allen-Bradley PLCs are among the most widely deployed industrial controllers in North America. They are found in:
- Water and wastewater treatment facilities across the US and internationally
- Electric power generation and distribution equipment
- Oil and gas processing infrastructure
- Municipal government systems including traffic management and public safety
- Manufacturing and food processing operations
Their ubiquity is precisely why they are targeted. A threat actor who understands how to operate Allen-Bradley PLCs using Studio 5000 has access to an enormous attack surface — because the same knowledge and tooling works across thousands of different facilities.
The critical enabler in all of these incidents was internet exposure. These PLCs were reachable from the public internet, which is not how they were designed to operate, and not how security best practices recommend deploying them. But the reality of critical infrastructure operations is that convenience often wins over security — remote monitoring, vendor access, and understaffed IT/OT teams create pressure to keep things reachable.
Shodan and similar internet scanning services make it trivially easy for threat actors to find internet-exposed PLCs. CyberAv3ngers almost certainly used exactly these tools to identify their targets.
Who Is at Risk
The CISA advisory identifies specific sectors at elevated risk:
Water and wastewater systems are the primary target in the confirmed incidents. Water utilities are particularly vulnerable because they frequently operate with legacy OT equipment, limited cybersecurity budgets, and small IT/OT teams. Many rural and municipal water systems have fewer than five dedicated IT staff.
Energy sector infrastructure — including electric utilities, natural gas facilities, and renewable energy operators — face the same exposure risks and are explicitly named in the advisory.
Government facilities and municipal systems — including local government networks with operational systems — have been confirmed targets.
Industrial manufacturing with Allen-Bradley PLC deployments should treat this advisory as directly relevant, even if not named in the initial disclosures. The attack technique is sector-agnostic.
If your organization operates Allen-Bradley PLCs and has any internet-facing connectivity in your OT environment, this advisory is addressed to you.
What the Advisory Requires You to Do
CISA AA26-097A includes specific technical mitigations. These are not aspirational recommendations — given the active exploitation confirmed in the advisory, they should be treated as urgent operational actions.
Immediate actions:
1. Identify all internet-exposed PLCs. Use your asset inventory, or if you don’t have one, use network scanning tools to identify any Allen-Bradley PLCs (or other industrial controllers) that are reachable from outside your network perimeter. Tools like Shodan can tell you what attackers already know — search for your own organization’s IP ranges.
2. Remove internet exposure. Any PLC that does not absolutely require internet connectivity should be isolated immediately. This means firewall rules, network segmentation, and if necessary, physically disconnecting external connectivity until proper controls are in place.
3. Change all default credentials. This is non-negotiable. Every Allen-Bradley PLC in your environment should have its factory-default credentials changed to strong, unique passwords. The CISA advisory explicitly identifies default credentials as a primary attack vector.
4. Enable authentication controls. Studio 5000 and the underlying ControlLogix/CompactLogix platforms support authentication mechanisms. Ensure these are enabled. Devices without authentication enabled are open by design.
5. Review HMI and SCADA displays for anomalous readings. If attackers have been in your environment, they may have manipulated display data. Validate that what your operators are seeing matches physical sensor readings.
Short-term actions:
6. Implement network segmentation. OT networks should be segmented from IT networks and from the internet. The PURDUE model provides a framework; the practical minimum is that PLCs should not be directly routable from corporate IT networks or the internet.
7. Enable logging and monitoring. Many OT environments have limited visibility into what traffic is traversing their networks. Industrial network monitoring tools (Claroty, Dragos, Nozomi Networks, etc.) can provide the visibility needed to detect unauthorized Studio 5000 connections.
8. Patch firmware where possible. Rockwell Automation has published firmware updates for affected product lines. Check the Rockwell Automation security advisories page for applicable patches for your specific PLC models.
9. Implement multi-factor authentication for any remote access to OT environments. VPN access without MFA is insufficient — if credentials are compromised, MFA is the last line of defense.
10. Contact Rockwell Automation’s PSIRT team if you believe you may have been targeted. They are working with CISA on incident response and can provide specific guidance for your deployment.
The Broader Strategic Context
This advisory does not exist in isolation. It is part of a pattern that has accelerated sharply in 2026.
In March, the South Pars gas field strike demonstrated that physical attacks on Iranian energy infrastructure have real geopolitical consequences. Iran’s cyber response — targeting Western water and energy systems — is the predictable asymmetric answer. The IRGC-CEC has long maintained that critical infrastructure attacks are a legitimate tool of state power, and CyberAv3ngers has been the operational arm of that doctrine.
Water infrastructure and power grid systems have been recurring targets throughout the conflict. What’s new in the April 7 advisory is the scale of confirmed incidents and the specificity of the technique — this is not opportunistic scanning, it is a deliberate campaign with a defined target set, a consistent method, and confirmed operational impact.
NERC has confirmed it is actively monitoring the grid in response to the advisory. The FBI has opened investigations into affected facilities. The EPA is providing technical assistance to water utilities.
What This Means for Security Leaders
If you are a CISO, security director, or IT/OT manager at any organization that operates industrial control systems — particularly in water, energy, or municipal sectors — the April 7 advisory should trigger several immediate conversations:
With your OT team: Do you know every internet-facing PLC in your environment? If the answer is “we think so,” that’s not good enough. You need an asset inventory you trust.
With your network team: Is your OT network segmented from your IT network? When did you last verify the firewall rules? Have you reviewed whether any firewall exceptions created for vendor or remote access have been left permanently open?
With your executive team: This advisory is a six-agency warning that a foreign state actor is actively attacking US infrastructure of exactly the type you operate. That is a board-level risk, not an IT department ticket.
With your vendors: Is your Rockwell Automation reseller or systems integrator aware of this advisory? Are they proactively reaching out to their customers? If not, that’s a conversation worth having.
The technique CyberAv3ngers is using requires no sophisticated cyber capability on your part to defend against. It requires closing an open door that should never have been open. The question is whether you know where your doors are.
Resources
- CISA Advisory AA26-097A — full text
- Rockwell Automation Security Advisories
- CISA ICS-CERT advisories for Allen-Bradley products
- WaterISAC threat intelligence for water sector operators
- E-ISAC for electric sector operators
This article reflects information available at the time of publication based on CISA Advisory AA26-097A and related reporting. Organizations should consult the original advisory and their sector-specific ISAC for the most current guidance.