When security researchers tallied ransomware incidents across all sectors in a single 30-day window in early 2026, the number for manufacturing stopped people mid-sentence: 89 confirmed attacks. Not in a quarter. Not in a year. In a month. That figure — drawn from dark web leak sites, incident disclosures, and threat intelligence feeds — signals something more than a bad stretch. It signals a structural shift in how ransomware gangs operate, and who they’ve decided is worth hunting.
Manufacturing has topped the IBM X-Force Threat Intelligence Index as the most-targeted industry for five consecutive years. In 2026, it accounted for 27.7% of all incidents observed by X-Force — more than finance, healthcare, and government combined in some quarters. The Dragos industrial cybersecurity report confirms the same trajectory: active ransomware groups targeting industrial sectors surged 49% year-over-year. The numbers aren’t noisy data. They’re a pattern.
This article explains why manufacturing has become the ransomware sector of choice, what’s changed in 2026, and what manufacturing CISOs and plant managers need to do about it right now.
Why Manufacturing? The Economics of Operational Pressure
Ransomware is a business. Like any business, attackers go where the return on investment is highest. Manufacturing checks every box.
Production downtime is unbearable. A ransomware attack on an IT system at a law firm might mean lawyers work from their phones for a few days. A ransomware attack that takes down a factory’s production line can cost tens of thousands of dollars per hour. When a single automotive plant goes dark, ripple effects hit suppliers, logistics partners, and just-in-time delivery commitments across the entire supply chain. Attackers know this. They price their demands accordingly.
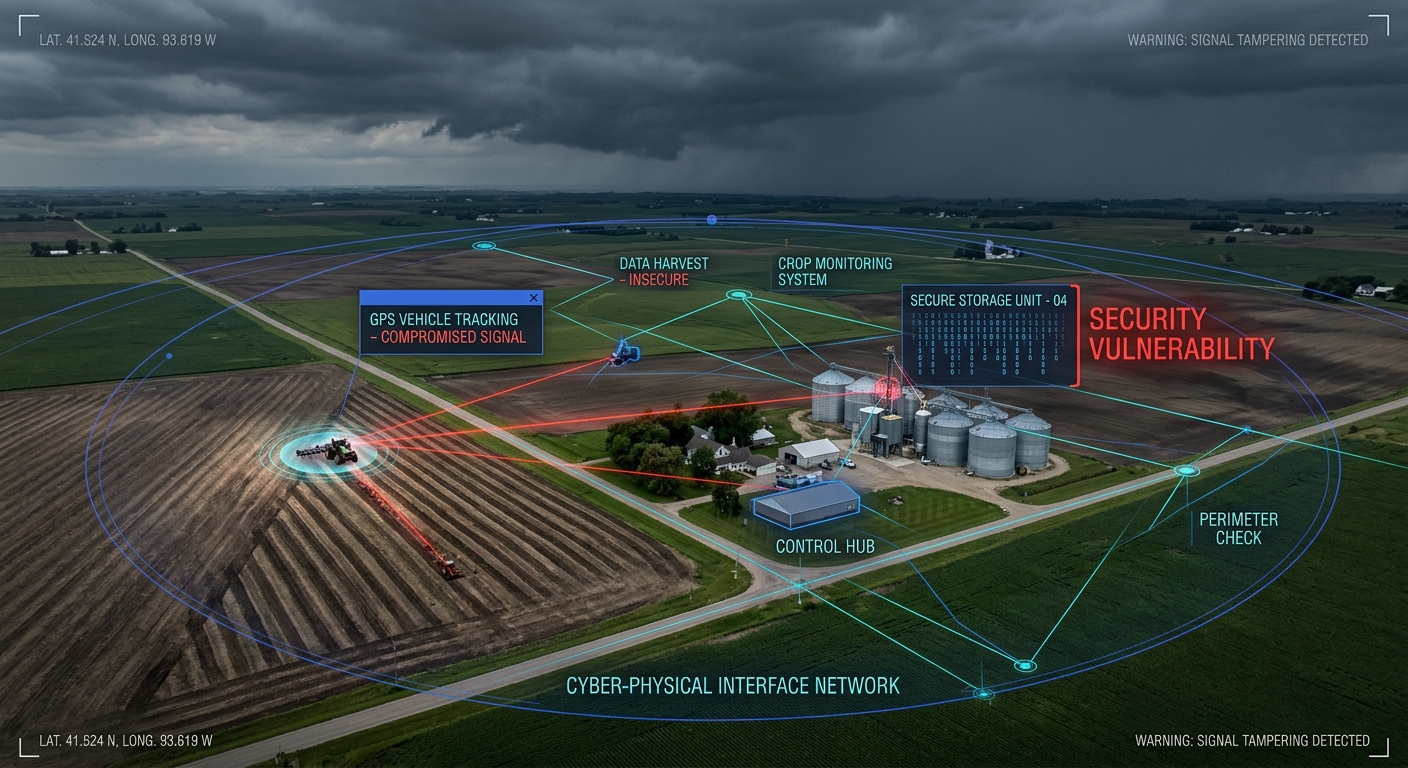
The IT/OT gap is a gift to attackers. Most manufacturing environments were built with operational technology (OT) — PLCs, SCADA systems, HMIs, distributed control systems — designed decades before cybersecurity was a consideration. These systems run on flat, unsegmented networks where IT and OT sit side by side. When ransomware breaches the corporate IT environment (via phishing, stolen credentials, or an unpatched VPN), it doesn’t stop at the office — it walks straight into the plant floor. The infamous NotPetya attack demonstrated this in 2017 when it destroyed systems at Merck, FedEx, and Maersk. In 2026, attackers are intentionally targeting that gap.
Intellectual property and supply chain leverage. Manufacturers carry proprietary process data, product designs, supplier contracts, and customer production schedules. A ransomware group that exfiltrates this data before encrypting systems can threaten to leak specifications, formulas, or customer lists — a double-extortion play that raises the pressure far beyond restoring operations. For companies with defense contracts or pharmaceutical production, the reputational and legal exposure of a data leak can exceed the ransom itself.
Legacy systems = unpatched attack surface. The average OT device in a manufacturing environment is 10-15 years old. Many run end-of-life operating systems (Windows XP, Windows 7) that haven’t received security patches in years. Vulnerability researchers have catalogued thousands of known, unpatched CVEs in common industrial control system components — and many of these are publicly available on dark web forums. A 2025 Forescout report named OT and network infrastructure as the fastest-growing attack surface in modern industrial organizations.
What Happened in 2026: The Attack Acceleration
The 89-attack figure isn’t an anomaly. It’s the culmination of a trend that accelerated sharply in 2025 and has continued into 2026.
Q3 2025: 72% of industrial ransomware cases. Data published by Industrial Cyber confirmed that manufacturing accounted for nearly three-quarters of all ransomware cases across industrial sectors in Q3 2025. Dragos attributed this partly to the democratization of ransomware tooling — AI-assisted attack platforms have lowered the skill floor for threat actors, meaning even mid-tier criminal groups can execute sophisticated multi-stage intrusions against OT environments.
The LockBit successor groups. Following law enforcement actions against LockBit in 2024, several successor and splinter ransomware-as-a-service (RaaS) operations filled the vacuum. These groups — including BlackSuit (formerly Royal), RansomHub, and Play — have explicitly prioritized manufacturing targets. RansomHub alone claimed 15+ manufacturing victims in the first 60 days of 2026. Their tactics include living-off-the-land techniques that evade traditional antivirus, targeting industrial engineering workstations, and exfiltrating OT environment documentation before deploying encryption.
The automotive sector under fire. Automotive manufacturers and their Tier 1/Tier 2 suppliers have been disproportionately hit. Just-in-time supply chains, complex ERP integrations with production systems, and global operations across dozens of jurisdictions create attack surfaces that are nearly impossible to fully harden. A single compromised supplier can provide lateral movement into a major OEM’s environment.
Pharmaceutical and food manufacturing targeted. Beyond heavy industry, pharmaceutical and food/beverage manufacturers have seen a surge in targeting. Attackers have discovered that production data in these sectors carries regulatory value — a ransomware group that threatens to corrupt batch records, tamper with quality control data, or leak pharmaceutical formulations can command multi-million dollar ransoms. The 2022 attack on Dole and the ongoing targeting of food processing facilities demonstrate that threat actors have no sector they consider off-limits.
The OT/ICS Targeting Shift: This Isn’t Your IT Department’s Problem
The critical change in 2026 is not just who is being attacked, but what attackers are going after. For years, ransomware deployed against manufacturing companies primarily encrypted IT systems — business networks, email, file servers, ERPs. Operational technology systems were sometimes collateral damage when flat networks allowed the malware to spread, but OT was rarely the deliberate target.
That has changed.
Dragos and other industrial security researchers have documented a clear shift: threat actors are now conducting reconnaissance of OT environments before deploying ransomware. They are mapping SCADA systems, identifying historian servers, enumerating PLC configurations, and in some cases staging payloads specifically designed to impact industrial control systems. This is Stage 2 ICS Kill Chain behavior — and while confirmed Stage 2 attacks remain relatively rare, the reconnaissance activity that precedes them is exploding.
Why does this matter? Because an attack that disables IT systems is recoverable in days or weeks. An attack that corrupts PLC firmware, wipes historian data, or triggers a controlled process shutdown can require months of recovery — and in some cases, physical hardware replacement. The potential for physical consequences (equipment damage, environmental releases, safety incidents) elevates these attacks from business disruption to critical infrastructure threats.
The Forescout 2026 Riskiest Connected Devices report explicitly calls out OT and industrial network infrastructure as becoming prime targets. Engineering workstations — the Windows machines used to program and maintain PLCs and HMIs — are now directly in ransomware groups’ crosshairs.
CISO Action Plan: What Manufacturing Security Leaders Must Do Now
The 89-attack figure is not background noise. If you’re a CISO, VP of IT, or plant manager in manufacturing, here is the prioritized action plan:
1. Map and segment your IT/OT boundary — immediately. The most impactful single action you can take is establishing a defensible IT/OT boundary. This does not mean an absolute air gap (most modern OEMs need some connectivity for remote monitoring and support). It means network segmentation, DMZs, and enforced data diodes between business networks and plant networks. Every manufacturing environment should know exactly where IT ends and OT begins — and that boundary should be monitored.
2. Take inventory of OT assets and their vulnerability exposure. You cannot protect what you don’t know about. Conduct a comprehensive OT asset inventory. Identify every PLC, HMI, SCADA server, historian, and engineering workstation. Map operating system versions. Flag end-of-life systems. Prioritize vulnerability remediation where patching is possible, and compensating controls (network segmentation, application whitelisting, enhanced monitoring) where it isn’t.
3. Implement OT-aware security monitoring. Traditional SIEM and EDR tools are blind to OT protocols (Modbus, DNP3, EtherNet/IP, OPC-UA). Deploy passive OT monitoring tools (Dragos Platform, Claroty, Nozomi Networks) that can detect anomalous behavior in industrial networks without disrupting production. Even basic anomaly detection — unusual connection attempts, unexpected configuration changes, new devices on the OT network — can provide early warning before ransomware deploys.
4. Test your backup and recovery posture for OT systems. Most manufacturing organizations test IT backup and recovery. Few test OT recovery. Do you have clean, recent backups of PLC programs, HMI configurations, and SCADA historian data stored offline and separately from the production environment? Can you restore them without internet connectivity? Ransomware operators know that organizations with poor OT recovery capabilities face maximum pressure. Remove that leverage.
5. Enforce multi-factor authentication on everything that touches your environment. Remote access to manufacturing environments — whether by internal IT teams, OEM service technicians, or third-party maintenance contractors — is a primary ransomware entry vector. Every remote access session should require MFA. VPN credentials are regularly sold on dark web marketplaces; MFA is the most cost-effective countermeasure against credential-based intrusion.
6. Run tabletop exercises that include OT scenarios. Most manufacturing organizations have business continuity plans. Few have tested what happens when ransomware reaches the plant floor. Run tabletop exercises that include OT impact scenarios: what happens if the historian goes down? If PLC programming workstations are encrypted? If the SCADA server becomes unavailable? This exercises your incident response team, identifies recovery gaps, and builds cross-functional muscle memory between IT security and operations.
7. Supply chain and vendor access hygiene. The automotive and semiconductor ransomware incidents of 2025 demonstrated that a Tier 1 supplier breach can cascade into OEM environments. Audit your vendor and supplier remote access. Establish minimum cybersecurity standards for vendors with network access to your OT environment. Consider requiring MFA, endpoint compliance verification, and session recording for all third-party remote maintenance sessions.
The Bottom Line
Manufacturing’s ransomware problem isn’t going to solve itself. The economics favor attackers — high ransom pressure, legacy OT exposure, fragmented IT/OT ownership, and low tolerance for downtime make manufacturers uniquely attractive targets. The 89-attack figure from a single 30-day window is a data point, but the trend it represents has been building for five years.
The good news: the countermeasures are known. IT/OT segmentation, OT asset inventory, industrial-aware monitoring, and disciplined backup practices are not exotic or prohibitively expensive. They require organizational commitment and cross-functional coordination — which, in manufacturing, means getting plant operations leadership bought in alongside the CISO.
The question for every manufacturing security leader right now is not whether their organization will be targeted. It’s whether they’ll be ready when it happens.
For resources on securing industrial IoT and OT environments in manufacturing, visit Secure IoT Office.
Sources: IBM X-Force 2026 Threat Intelligence Index; Dragos 2026 ICS/OT Cybersecurity Year in Review; Forescout 2026 Riskiest Connected Devices; Industrial Cyber Q3 2025 ransomware analysis; Breached.Company 2026 ransomware tracking data.