This morning, Bahrain announced that an Iranian drone strike damaged one of its desalination plants. Hours earlier, Iran claimed the US struck a desalination facility on Qeshm Island, cutting water supply to 30 villages.
In the span of 24 hours, water infrastructure went from “soft target everyone avoids” to “active battleground.”
For security professionals protecting industrial IoT and operational technology environments, this escalation should trigger immediate reassessment. The same Iranian actors now launching physical strikes on water infrastructure have been inside American water systems since at least 2023.
The Desalination Escalation
What Just Happened
March 8, 2026:
- Bahrain’s Interior Ministry announced an Iranian drone attack damaged a water desalination plant
- Iran’s Foreign Minister Abbas Araghchi claimed a US airstrike hit a desalination plant on Qeshm Island in the Strait of Hormuz
- Araghchi warned: “The U.S. set this precedent, not Iran”
This matters because Persian Gulf nations depend entirely on desalination. There is no backup. No aquifer. No alternative water source for millions of residents.
As one analyst noted in Fortune this week: “Everyone is watching oil in the Iran war, but the real risk is water.”
Why Desalination Plants Are Different
Unlike oil refineries or power plants, desalination facilities:
- Cannot be replaced quickly — construction takes years
- Have no stockpile — you can’t store months of drinking water
- Serve entire populations — not just industry
- Are increasingly IoT-connected — for efficiency and remote monitoring
A serious attack on Gulf desalination infrastructure wouldn’t just damage commerce. It would create a humanitarian catastrophe in days.
The Cyber Dimension: Iran Has Been Practicing
Here’s what makes this escalation particularly concerning: Iranian state actors have been actively targeting water infrastructure for years.
CyberAv3ngers: The IRGC’s Water Campaign
In December 2023, CISA issued an urgent advisory (AA23-335a) warning that IRGC-affiliated hackers had compromised water utilities across multiple US states.
The group, known as CyberAv3ngers, left messages on compromised systems:
“You have been hacked, down with Israel. Every equipment ‘made in Israel’ is CyberAv3ngers legal target.”
How did they get in? Default passwords on internet-exposed PLCs.
The targeted devices were Unitronics Vision Series programmable logic controllers — the same systems controlling:
- Chemical dosing
- Pressure monitoring
- Pump operations
- SCADA interfaces
The Oldsmar Precedent
The most infamous US water attack happened in February 2021 in Oldsmar, Florida. Someone remotely accessed the water treatment plant’s systems and attempted to increase sodium hydroxide (lye) levels to dangerous concentrations.
An operator watching the screen in real-time caught the intrusion and reversed the changes. But the attacker had been inside the system for 3 to 5 minutes.
The investigation never publicly attributed the attack, but one theory that emerged: Iranian hackers selling access to a Florida water treatment plant.
CISA’s Growing Concern
Throughout 2024 and 2025, CISA documented Iranian reconnaissance and intrusion attempts at water utilities serving major metropolitan areas. The pattern was consistent:
- Scan for internet-exposed OT devices
- Try default credentials
- Establish persistence
- Wait
That “wait” phase is what should worry you. Pre-positioned access in critical infrastructure isn’t about immediate disruption — it’s about having options when conflict escalates.
We’re now in that conflict.
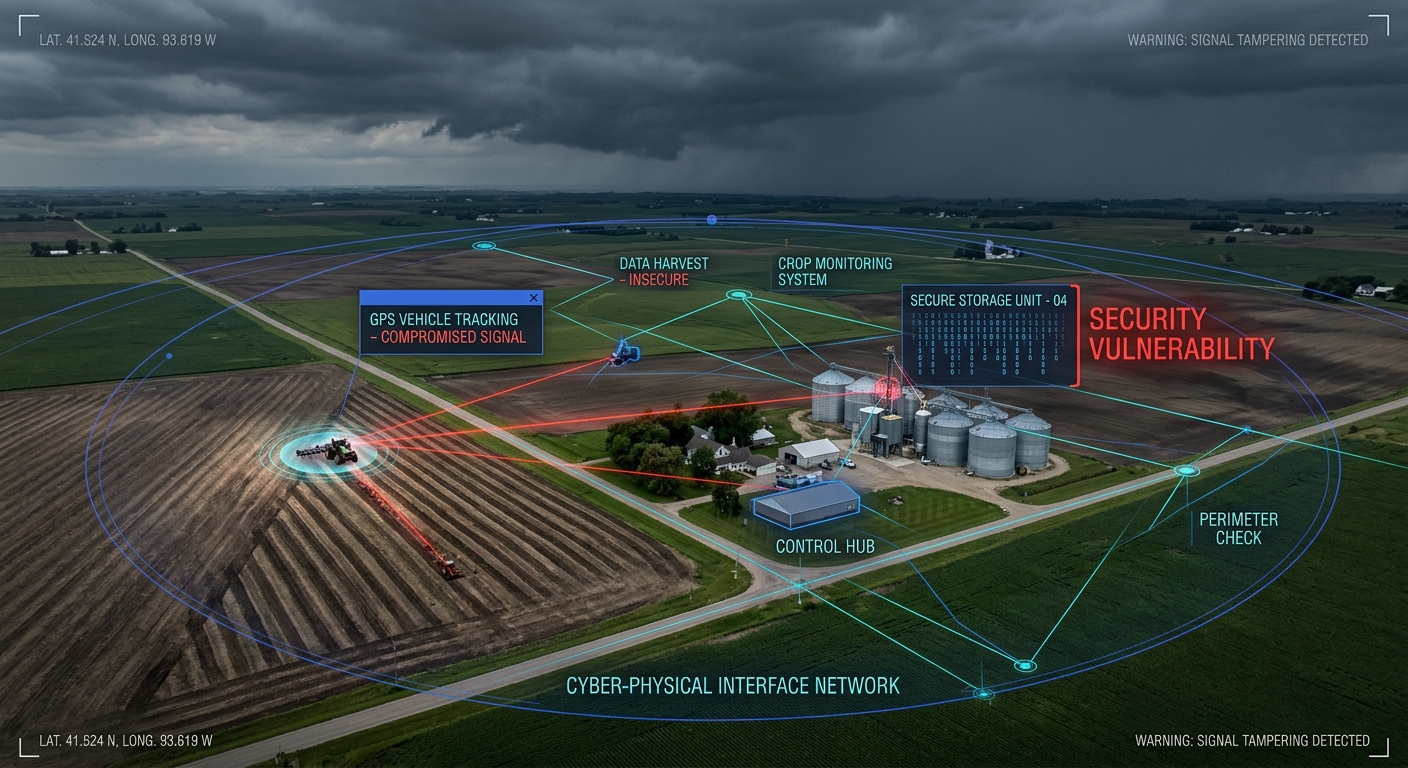
What This Means for Enterprise IoT Security
You might think this doesn’t apply to your organization — you’re not running a municipal water plant. But consider:
Water Systems Are Everywhere
Modern commercial facilities increasingly manage their own water infrastructure:
- Cooling systems for data centers and manufacturing
- Process water for pharmaceutical and food production
- Fire suppression systems in high-rise buildings
- Irrigation for large campuses and agriculture
All of these systems are being connected for monitoring, efficiency, and remote management. All of them use similar industrial controls. Many have the same vulnerabilities.
The Same Attackers, The Same TTPs
The tactics that worked against municipal water plants work against commercial water systems:
| Attack Vector | Municipal Impact | Enterprise Impact |
|---|---|---|
| Default PLC credentials | Chemical dosing manipulation | Cooling system sabotage |
| Internet-exposed SCADA | Pump control hijack | BMS compromise |
| Unpatched HMI software | Ransomware deployment | Production shutdown |
| Flat OT networks | Lateral movement to IT | IT/OT convergence breach |
Iran’s Expanded Target List
Unit 42’s March 2026 threat brief notes that Iranian state-aligned threat actors are targeting:
- Supply chains of adversary organizations
- Critical infrastructure broadly defined
- Vendors and providers serving priority targets
If your organization does business with defense contractors, government agencies, or Israeli companies, your water systems (and all other OT) should be on heightened alert.
Immediate Actions
1. Inventory Your Water-Related Systems
Do you know every system that touches water in your facilities?
- Cooling towers and chillers
- Water treatment for manufacturing processes
- Building management systems controlling water
- Irrigation and landscaping automation
- Fire suppression system controls
2. Check for Default Credentials
This sounds basic because it is. But it’s still the #1 entry point for Iranian water system attacks.
# Common default credentials on water system PLCs
# If any of these work on your systems, you have a critical vulnerability
admin/admin
administrator/1234
1111/1111
guest/guest
3. Verify Network Segmentation
Your OT systems controlling water should NOT be:
- Directly accessible from the internet
- On the same network segment as corporate IT
- Reachable from guest WiFi or contractor networks
4. Enable Logging and Monitoring
You can’t detect what you can’t see. At minimum:
- Log all remote access to water system controls
- Alert on configuration changes to PLCs
- Monitor for unusual communication patterns
5. Review Vendor Access
Many water system attacks exploit remote access tools used for vendor support. Know who has access and how.
The Bigger Picture
The 2026 Iran conflict has made something explicit that security professionals have understood for years: water infrastructure is a legitimate military target.
The Bahrain desalination strike isn’t an outlier — it’s a preview. Both physical and cyber attacks on water systems will intensify. The actors who’ve been quietly pre-positioning inside US water infrastructure now have clear motivation to act.
For enterprise security teams, this means:
- Water systems are critical infrastructure — treat them that way
- Iranian threat actors are active — and their TTPs are well-documented
- The attack surface is expanding — IoT connectivity creates new vulnerabilities
- Detection matters more than prevention — assume breach, focus on visibility
The war in the Middle East may feel distant. The threat to water infrastructure is not.
Related Coverage:
- The Cyber War in the Shadows: How the 2026 Iran–Israel–U.S. Conflict Is Reshaping the Middle East’s Digital Battlefield
- Banned at Dawn, Deployed by Dusk: The U.S. Used Anthropic’s Claude in the Iran Strikes — Hours After Trump Banned It
Monitoring water infrastructure threats? Share your insights with us at CISO Marketplace.