On March 4, 2026, Iraq went dark.
“The power grid has completely shut down across all Iraqi provinces,” the electricity ministry announced. Sirens blared at the US Embassy in Baghdad. Hospitals scrambled for backup generators. Traffic lights failed across cities of millions.
The official cause: “technical fault.” The timing: four days into a regional war involving cyberattacks on critical infrastructure.
Meanwhile, Iran’s internet had already collapsed to 1-4% of normal levels, cutting off communication, banking, and the digital infrastructure that modern societies depend on.
This is what happens when power grids become targets. For smart cities and IoT-dependent enterprises, it’s a preview of cascading failure.
The Pattern: Power Grid Targeting in Modern Conflict
Iraq Blackout — March 4, 2026
The Iraqi government attributed the nationwide blackout to a “sudden drop in gas supply.” But the context matters:
- The blackout occurred during active military operations in the region
- Reports emerged of an Israeli cyberattack on Iraq’s main power plant
- The timing coincided with Iranian missile and drone attacks on Gulf states
Whether the immediate cause was cyber, kinetic, or cascading failure from regional instability, the result was the same: 44 million people without power.
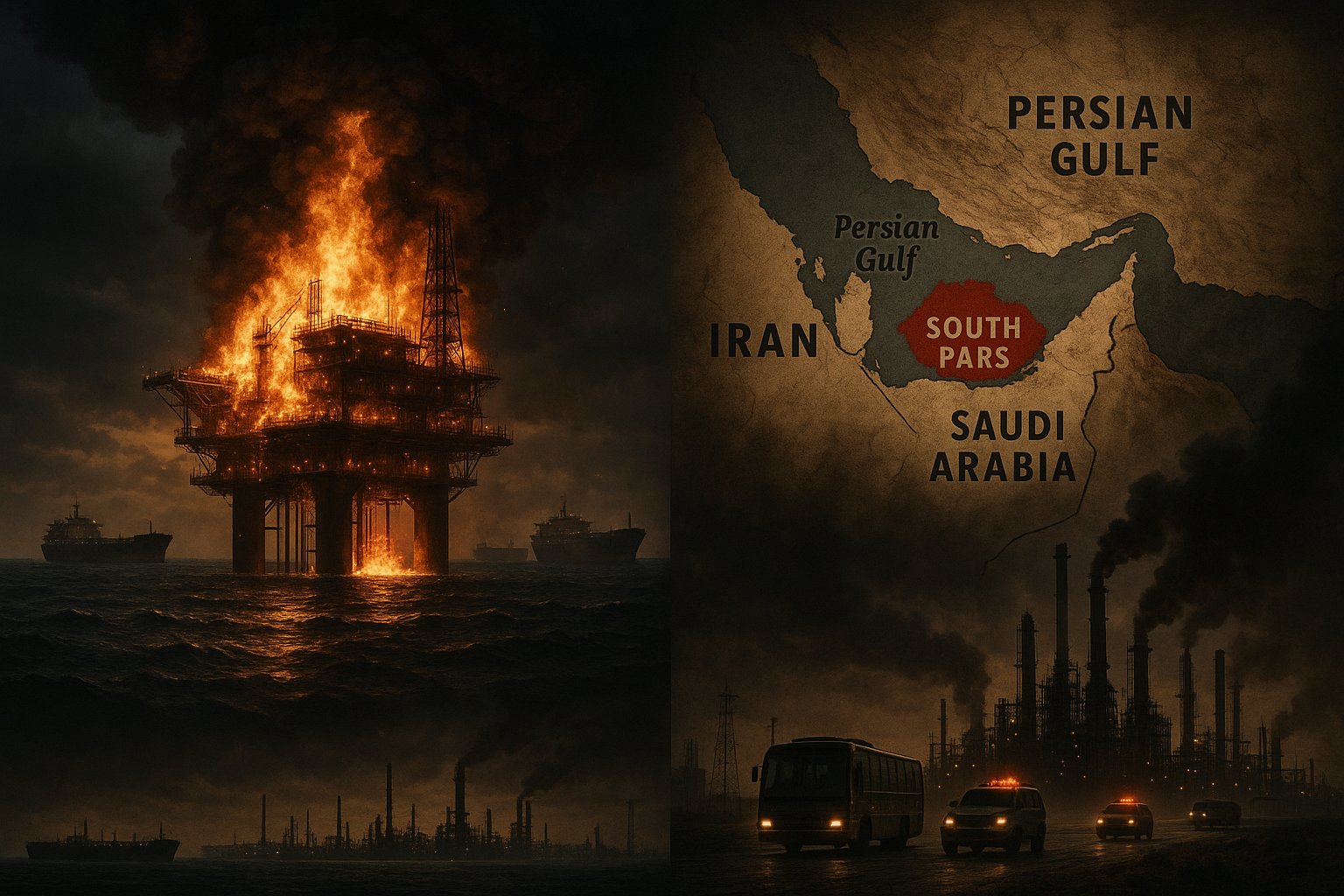
Iran’s Near-Total Connectivity Collapse
When US and Israeli strikes began on February 28, Iran’s internet dropped to between 1% and 4% of normal levels according to NetBlocks monitoring.
This wasn’t just an inconvenience. It meant:
- No digital banking — economic paralysis
- No communication apps — families couldn’t contact each other
- No news access — information vacuum filled by rumor
- No IoT functionality — smart infrastructure became dumb
The connectivity loss was so severe that Iran’s government eventually admitted it had intentionally restricted internet to “reduce cyberattacks” — essentially sacrificing its own digital economy to prevent further compromise.
The Venezuela Playbook
We’ve seen this pattern before. In January 2026, during Operation Absolute Resolve that captured Venezuelan President Maduro, coordinated cyberattacks on Venezuela’s power grid preceded the kinetic operation.
The sequence:
- Power grid disruption — lights out across regions
- Communication blackout — no radar, no coordination
- IoT collapse — smart city systems fail
- Kinetic operation — forces move in the dark
As we covered in our analysis of Operation Roaring Lion, this combination of cyber and physical operations has become doctrine.
No Power, No Smart City
Here’s what most smart city planners don’t adequately model: cascading IoT failure during extended blackouts.
First Hour
- Traffic management systems fail
- Building access controls go to fail-open or fail-closed
- Emergency dispatch systems switch to backup power
- Security cameras stop recording
First Day
- Cell towers begin dropping off as batteries drain
- Water pumping stations struggle without power
- HVAC systems in critical facilities overheat
- Refrigeration fails in hospitals and food supply chains
First Week
- Generator fuel runs out for non-priority facilities
- Sewage systems back up as pumps fail
- Payment systems completely collapse
- Social order begins deteriorating
This isn’t hypothetical. It’s what happened in Puerto Rico after Hurricane Maria. It’s what happened in Texas during the 2021 freeze. And it’s what’s happening right now in conflict zones where power infrastructure is targeted.
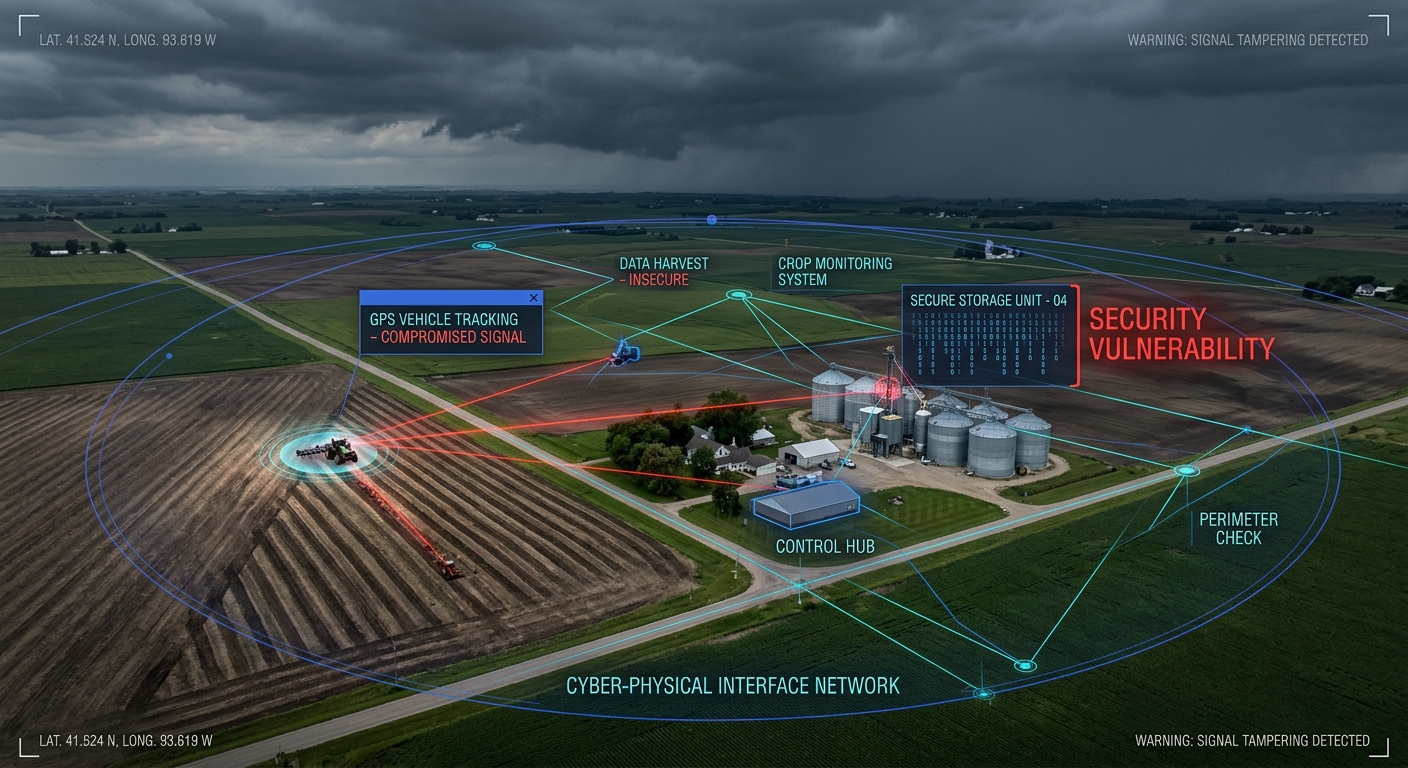
The Cyber-Physical Attack Chain
What makes modern power grid attacks particularly dangerous is the combination of cyber and physical methods.
Step 1: Reconnaissance and Pre-Positioning
Iranian, Russian, and Chinese threat actors have been mapping Western power infrastructure for years. CISA has documented:
- Persistent access to US energy sector networks
- Reconnaissance of Industrial Control Systems (ICS)
- Exploitation of internet-exposed SCADA systems
- Pre-positioned malware waiting for activation
Step 2: Cyber Disruption
When conflict begins, pre-positioned access enables:
- Protection relay manipulation — causing physical damage to equipment
- Load balancing disruption — triggering cascading failures
- SCADA system lockout — preventing operator response
- Data destruction — eliminating recovery options
Step 3: Physical Follow-Through
As we’re seeing in the 2026 conflict:
- Strikes on power generation facilities
- Attacks on transmission infrastructure
- Targeting of fuel supply chains
- Combined effects creating extended outages
Implications for Enterprise IoT
If you’re running smart building systems, industrial IoT, or any infrastructure dependent on continuous power and connectivity, the 2026 conflict offers clear lessons.
1. Your Backup Power Isn’t Enough
Most enterprise backup power is designed for hours, not days or weeks.
Assessment questions:
- How long can your critical systems run on backup power?
- What’s your generator fuel supply chain look like?
- Do you have agreements in place for fuel priority during regional emergencies?
- Have you tested extended blackout scenarios?
2. Your IoT Systems Have Hidden Grid Dependencies
Many “air-gapped” OT systems have unexpected dependencies:
| System | Hidden Dependency |
|---|---|
| Building access control | Internet for cloud management |
| Industrial sensors | Cellular backhaul for data |
| Security cameras | PoE from grid-powered switches |
| HVAC controls | Cloud-based optimization |
| Inventory systems | Continuous connectivity for updates |
3. Graceful Degradation Is a Design Choice
Smart systems should fail safely. But most don’t.
Key design questions:
- What happens to your access control when power fails?
- Do your industrial processes have manual overrides?
- Can your building management operate in offline mode?
- Do your employees know manual procedures?
4. Regional Disruption Affects You Even If You’re Not Hit
The Iraq blackout didn’t just affect Iraqi facilities. It disrupted:
- Supply chains passing through the region
- Communication with personnel in-country
- Contractor operations for multinational companies
- Data center operations in the Gulf
Defensive Priorities
For Smart City Operators
- Harden power sector cybersecurity — OT segmentation, monitoring, incident response
- Ensure manual override capability — systems must work without digital controls
- Stockpile critical supplies — fuel, water, medical supplies for extended outages
- Communication resilience — satellite, radio backup for when cell networks fail
- Cross-sector coordination — power, water, transport, health must plan together
For Enterprise IoT Teams
- Map your grid dependencies — know exactly what fails when power goes
- Test extended outage scenarios — not just hours, but days
- Implement offline operation modes — critical systems should degrade gracefully
- Review third-party dependencies — your cloud provider’s generator isn’t your generator
- Plan for regional disruption — even distant conflicts affect global supply chains
For Security Operations
- Monitor for reconnaissance — energy sector targeting often precedes attacks
- Assume pre-positioning — threat actors may already have access
- Coordinate with utilities — information sharing is critical
- Prepare for cascade effects — a power outage may be the first domino
The Reality Check
The 2026 Iran conflict is demonstrating something security professionals have warned about for years: power grid attacks are not theoretical.
The Iraq blackout affected 44 million people. Iran’s connectivity collapse paralyzed the country’s digital infrastructure. Desalination plants on both sides have been struck, threatening water supplies.
These aren’t edge cases. This is the new normal of modern conflict.
For organizations running smart buildings, industrial IoT, or any infrastructure dependent on continuous power, the question isn’t whether grid attacks could happen in your region. It’s whether you’re prepared when they do.
Related Reading:
- When Water Becomes a Weapon: Critical Infrastructure Under Fire in the 2026 Iran Conflict
- Operation Roaring Lion: The Cyberattack That Rewrote the Rules of Modern Warfare
- The Cyber War in the Shadows: How the 2026 Iran–Israel–U.S. Conflict Is Reshaping the Middle East’s Digital Battlefield
Building resilient IoT infrastructure? Connect with us at CISO Marketplace.